We consider only a subset of transactions in this dataset. The resulting dataset consists in transactions between entities, that group together clusters of Bitcoin addresses. The raw dataset consists in transactions between Bitcoin addresses, which is initially preprocessed by Chainalysis Inc. (see Section S2). Moreover, we do not have information about which users trade with other users on the same DWM.
Stolen Credit Cards And Data
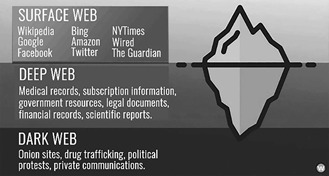
This online marketplace created unique opportunities and risks for its users, driving the intricate dynamics of illicit trade. The Silk Road was a pioneering platform that operated in the deep web, serving as an online marketplace for various goods and services. These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack. These hidden markets promise anonymity, but in practice, users often slip up. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records. What’s the difference between classic marketplaces and data stores?
Other Ways To Access Dark Web Platforms
Several Darkweb practices involving technologies are more advanced than those on the surface web, especially regarding privacy-protecting practices while retaining certain aspects of professional surface web services. Using DUTA, they compared two text representation techniques and three supervised classifiers to categorize Tor hidden services. The authors find that computer worms and scanning activities are the most common threats investigated through the Darknet, but DDoS amplification and spoofing activities are understudied. They define and characterize the Darknet, compare it to other monitoring systems, and report on case studies.

Agentic AI–Driven Threat Intelligence Tailored For Every Function
The downside is that it limits data to only 25mbps per user. The platform is protected from government interference and malicious attacks to protect the user. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. Using the ProtonMail .onion site offers security and privacy advantages.
Industry-Specific Cyber Threat Intelligence Powered By Agentic AI
This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web. The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services. Launched in April 2021, MGM Grand Market is a dark web marketplace that focuses on the sale of counterfeit goods, stolen financial data, and a range of illicit digital products. The Russian Market has been around since 2019 and is one of the more prominent dark web marketplaces. Mega Market is known for its user-friendly interface and high security, including support for PGP encryption and two-factor authentication.
Step 2: Find The Official TorZon URL
- At TecnetOne, we offer a specialized cyber-patrolling service for businesses, designed to continuously monitor these hidden spaces.
- Despite how big the dark web forum market is, or how many people it attracts, these forums remain a risk to both individual users and businesses.
- SecMail is one of the most popular email services on the dark web.
- Archetyp was Europe’s longest running and bloodiest market in the 2020s.
- Despite being under legal scrutiny, Cracked.io remains one of the key hubs for those involved in cybercrime activities.
- As its name suggests, this forum functions as a massive, ever-updating library of stolen databases, blending older leaks with freshly dumped data.
You must be aware of the risks of investing in forex, futures, and options and be willing to accept them in order to trade in these markets. You must be aware of the risks and be willing to accept them in order to invest in the futures, FOREX and CFDs markets. Master a proven methodology and turn your chosen trading platform into a true engine for profitability by visiting Colibri Trader. This is the ultimate key to shifting from simply participating in the markets to consistently profiting from them.
I2P (Invisible Internet Project)
Key characteristics of the Darkweb include the inability to search or list them through legal platforms, passwords to gain entry when accessible, and hidden identities of users, network traffic, IP addresses, and data exchanged through them . As with many other darknet marketplaces, TorZon operates on the Tor network, ensuring that its users remain invisible and their activities secret. As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created. Deep web marketplaces are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity of the dark web. Investors will appreciate Webull’s comprehensive and user-friendly desktop and mobile platforms, which offer charting and custom trading tools. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
The anonymity provided by the deep web utilized advanced encryption and privacy measures, drawing users who sought to navigate the less regulated digital economy. Throughout its operation, the Silk Road underwent notable growth in transaction volume, driven by various factors including user trust, product diversity, and anonymity features. The Silk Road, largely recognized as a significant marketplace within the deep web, showcased a diverse array of transactions. In various ways, the historical significance of the Silk Road resonates with the modern notion of the deep web as an underground marketplace. Through statistical analysis, the article presents data on Silk Road transactions, shedding light on its user demographics and the reasons behind its popularity. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want.

This can lead to a biased view of the research landscape, as papers not included in the database will not be included in the analysis. These databases may include only some relevant papers, particularly those published in less well-known or less prestigious journals or languages other than English . A further limitation of bibliometric analyses that rely on abstract databases such as Scopus or Google Scholar is that the coverage of these databases may need to be completed. The search terms should be narrow enough for the resulting data to reflect the research on a particular topic accurately. First, bibliometrics can be influenced by factors such as the prestige of the journals in which research is published, the language in which it is written, and the number of authors on a paper .
Users in such stable pairs turn out to be the ones with the largest trading volume on DWMs. His contributions focus on expanding encryption tools, promoting crypto-anarchist philosophy, and pioneering projects centred on leveraging cryptography to protect the privacy and political freedoms of others. This means it’s sometimes possible to buy these currencies (such as XMR) in exchange for fiat (GBP, USD, AUD, etc), but you may find yourself prevented from transferring such currencies outside of the platform you’ve purchased them from. Some get hacked, some get shut down by law enforcement, and some succumb to their own greed – whereby the operators ‘exit scam’ entire communities. It’s occupied by people from all walks of our complex and layered lives – from outright criminals and troublemakers, to journalists, dissidents, and security researchers (like myself).
The Hidden Wiki
Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. Here are some of the common dark web dangers that users can face. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. All in all, it is not illegal to access the dark web, but it can create issues for you.
Is Using The Tor Network Illegal?
Finally, we note that the same user can interact in multiple DWMs12,13. They may be attributed to a residual amount of Bitcoins in an address or transactions between two business partners where no good is actually given in return, respectively. We discard single Bitcoin transactions below $0.01 or above $100,000, which are unlikely to show real purchases and minimise false positives. Additional considerations on our data and methods are available in Section S1. The reasons for the differential impact of COVID-19 on U2U trading vs. DWM trading are difficult to pin down. By contrast, trading volume on DWMs was negatively affected by COVID-19, mainly due to shipping delays37,38.



