We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. As you can imagine, bad actors around the world would be attracted to any method of keeping their illegal activities undercover, and began to appreciate the dark web as a place to more or less safely conduct their activities. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions.
Step 3: Strengthen Your Security And Anonymity
Each search engine opens the door to potentially harmful content, making caution a necessity. However, that means that the most important content for dark web filtering, such as threat actor communications or early-stage data leaks, can be missed entirely due to over-filtering. However, while it may help users find basic links organized by topic, it offers no actual search functionality or dynamic indexing. Many links found there are outdated or broken, and it provides very little metadata or context for search results.
But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
Some are so well-built that they appear trustworthy until it’s too late. Many surface web results claiming to link to the “real” Hidden Wiki are actually trap sites. But instead of protecting whistleblowers, these fakes are designed to collect sensitive documents or deanonymize users through malicious code. These clones mimic the design and purpose of the original, often going so far as to copy privacy statements and security warnings.
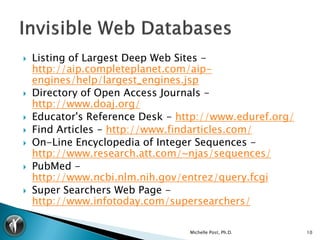
Resources
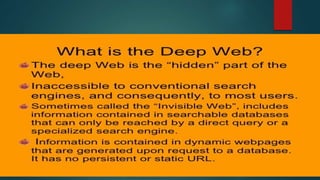
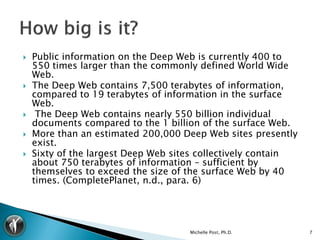
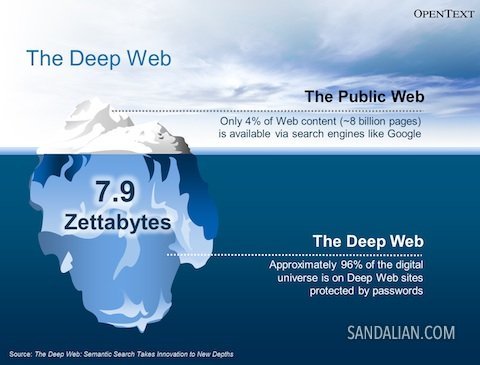
Google’s purpose is to show the most relevant information to all of its users quickly and easily. Perhaps the best-known tool used to access the dark web is the Tor browser. The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search.
Browsing The Dark Web With Tor
It’s free, open-source software, specifically designed to protect user anonymity through layered encryption. On the other hand, the dark web is a smaller section of the deep web that requires special software or configuration, like the Tor browser, to access. Moreover, it has clean, categorized results for research, forums, privacy tools, and file-sharing. It is essential to verify the links posted on it before you visit any, always. Tunnels is ideal for those who want secure, private conversations online.
Subscribe To Our Newsletter!
- The dark web exists on encrypted networks and uses protocols that traditional search engines like Google or Bing can’t access.
- Researchers, investors, and enthusiasts rely on Blockchain.com’s data to understand market trends, making informed decisions based on comprehensive blockchain information.
- Stick to verified dark web directories and legitimate services to minimize your exposure to risks.
- Then, a part of the deep web is the dark web which is only accessible through special software and tools.
- When you use Hidden Wallet, you bypass this problem and can purchase with complete anonymity.
In addition, Ahmia and Haystack make every effort to filter out and blacklist sites known to contain harmful, abusive, or illegal content. Many of those sites are listed because their devs have submitted the site directly to the search engine for indexing. You can use this community-edited link database to find everything from anonymous chat rooms, to Dark Web social networks, and blogs about various interesting subjects.
Dread went offline for several months due to DDoS attacks in 2022 but it’s back up and running now. You can also just go to explore what’s going on in the anonymous crowd. You can go there to get answers to any questions you might have and stay completely anonymous. A good service protects your identity by encrypting your data. However, certain countries outlaw anonymous browsing in general.
For example, you can try DuckDuckGo’s .onion version, though it has a limited selection of dark web sites. So, it’s difficult to determine when a popular .onion site is going to disappear or go offline. Subgraph OS is a hardened Linux distribution for secure, anonymous communication.
Is DuckDuckGo An Actual Dark Web Search Engine?
OnionLinks is a library of dark web links, most importantly, active links. But it is not all bad; the dark web’s anonymity also allows well-meaning individuals, such as whistleblowers As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. We’ve organized these sites into intuitive categories so you can quickly jump to what matters most for you.
DarkNet Army
The Dark Web is the part of the internet that one accesses using a particular tool. The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe. Engaging in illegal activities (like buying drugs, weapons, or stolen data) is illegal. Search engines do not index these sites and use domains like .onion (for Tor) or .i2p (for I2P). Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity.
No, .onion sites require the Tor network to access them. Yes, if you’re using tools like Tor, a VPN, and avoiding suspicious links, these search engines can be safe when used responsibly. In this blog, we explore the top 10 Dark Web search engines of 2025, focusing on safety, anonymity, and usability.
It is an archive stored on the Dark Web that keeps a snapshot of websites on the surface internet. These sites are intentionally hidden to protect the privacy and anonymity of both the site operators and visitors. The dark web consists of websites that use encrypted .onion domains, which require specific software and protocols to access.
Just as you explore hidden corners of the internet, you need to secure your data on the go. For example, whistleblower platforms such as SecureDrop use onion websites to securely transmit confidential information to journalists without revealing the source’s identity. Onion websites are therefore caught between the legitimate desire for privacy and the challenges that arise from their misuse.The dark web, accessible through onion websites, is a double-edged sword. This entire process ensures that the Tor network itself does not need a central directory of .onion sites. However, this same anonymity also makes onion websites a breeding ground for illicit activities. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.
The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. The deep web is basically all the content that you can’t find using Google or Yahoo search. That means that only 0.024% of all the known pages are findable in Google’s search engine. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). In addition, the content on the pages don’t need any special or custom configuration to access.
While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The downside is that it limits data to only 25mbps per user. SecMail is one of the most popular email services on the dark web. Even without the code, you can visit the security section to get tips on improving your daily life privacy.
One of the oldest and most robust dark web search engines, the Torch search engine is known for being fast, straightforward, and acting as an unblocked search engine with minimal filtering. Operating through Tor, DuckDuckGo provides a non-censored search engine experience without logging personal data. The Ahmia search engine is widely appreciated for its clean design and focus on legal, safe content. Onion search engine has made it easy for people to rely on content exploration without possessing advanced technical skills.
Nope, we do not know the websites or links for all the content we need, rather we key-in a keyword on a search engine, get millions of results, click on any of them to reach a website. Additionally, there are lists of curated onion sites that users can access in a single click – providing a safer way to find working and verified tor links, while also preventing the user from clicking on broken links or malware pages. To access .onion websites securely, you’ll need the Tor Browser, a privacy-focused tool designed specifically for anonymous browsing. These sites can’t be found using ordinary search tools—they require specific dark web search engines and special browsers, primarily Tor, designed for anonymity and security.



