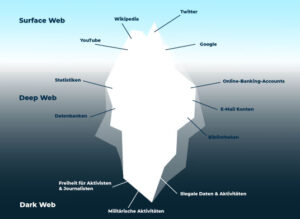
This section explores the security practices of our top 10 darknet rankings as of February 27, 2025,...
darknet
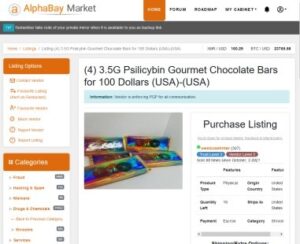
The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really...
The emphasis on anonymity ensures that transactions remain untraceable, a hallmark of the darknet marketplace. Australian darknet...
These officers must have a strong understanding of law, the Internet, human rights, privacy, communication technologies, cryptocurrencies,...
In April, TheRealDeal, the first open cyber-arms market for software exploits as well as drugs, launched to...
It’s the place where you can buy or sell stolen credit card numbers, SSH login credentials, and...
Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its...
They often sell across multiple markets or operate standalone storefronts via encrypted apps like Telegram and Signal....
Look for well-established users with a history of positive contributions, and check the consistency of information shared...
Contact moderators via the market’s system (e.g., Abacus’s 36-hour resolution)—provide order details, PGP-signed proof, and screenshots. They...