And while both Tor and VPNs provide security and privacy, I think VPNs are better because Tor has some security issues. I personally think the Tor browser is only good for surfing dark web links, while VPNs have many more use cases — they’re great for streaming, torrenting, gaming, and bypassing censorship. That’s because Tor’s speeds are pretty slow and its bandwidth is limited, so torrenting over Tor will cause even more slowdowns.
How Can I Differentiate Legitimate Services From Scams On The Dark Web?
It routes internet traffic through a series of relays and encryption layers, making it extremely difficult to trace a user’s online activities. These websites are not indexed by search engines and can only be reached through the Tor network. It’s important to remember that anonymity does not equate to invincibility, and law enforcement agencies actively monitor and investigate illegal activities on the dark web. It’s worth noting that even if accessing the dark web is legal in your country, engaging in illegal activities can have severe consequences, both legally and ethically.
The Tor browser is notorious for providing a secure browsing experience and allowing access to the d… While it is not illegal to access it, the illicit activities that mainly occur there can harm anyone who doesn’t know them. While accessing the dark web is indeed possible, following these tips can help you remain secure and anonymous while browsing the dark net. However, even using some of the best online security tools, you can still be vulnerable if you don’t remain vigilant with your browsing habits.
Beginners & Casual Users
Only the site publisher is protected when accessing onion sites using a proxy, meaning all your browsing information is visible to the server. If you’ve ever snooped around on the internet, you may have encountered the term “onion sites” or “Tor.” Onion sites are unindexed websites on the dark web that can be accessed using the Tor Browser. The existence of an anonymous and hidden internet then allowed for alternative information channels and illegal websites to flourish. When you use Tor, which routes your internet traffic through many different relay nodes, your online activity is obscured because you’re browsing anonymously.
Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information. Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web. Among them was a Paraguayan man they believe was the network’s ringleader. In the operation, police dismantled multiple pedophile chat sites, detaining four suspects. Law enforcement agencies frequently target sites that distribute child pornography. Bitcoin allows for anonymous donations, making it easier for terrorists to fund their activities and purchase weaponry.
Is Tor Browser Free?
A VPN conceals this access and will protect you from unwanted trouble. Tor is designed to keep users anonymous, although there can never be any guarantees in life. By the time it reaches its destination, your real IP address is buried so deep that tracking you becomes nearly impossible.
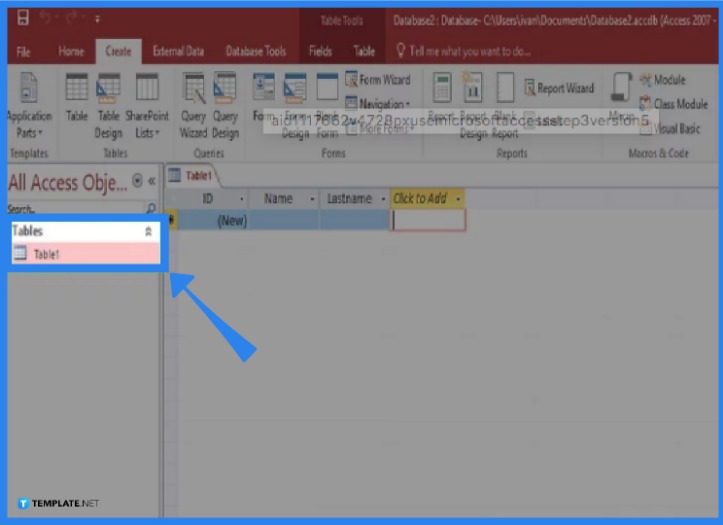
Black Ops 7 turns its story mode into a live co-op service, with strict online rules that hit solo players hardest. Because of this reason, it is quite easy to encounter fraudulent or malicious websites and you need to take a cautious approach to manually avoid them. By traditional websites, we mean websites with domains like .com, .org, .gov, etc., and easy-to-remember names, like google.com. Dark Web also does not have traditional websites like you find on the Surface web. Turn on your VPN and launch the Tor browser and it will automatically connect to the Tor network from which you can access the Dark Web anonymously.
Why Use The Tor Browser With A VPN
The surface web is what you access with Chrome, Firefox, or Safari. Underneath it are deeper layers that aren’t visible through normal browsing. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion. Whether you’re here out of curiosity or necessity, these steps will help you browse without getting burned. You’ll learn how to set up Tor Browser the right way, spot legit .onion links, and follow key safety checks to stay private.
- In contrast to the deep web, safely accessing the dark web is not as easy.
- DuckDuckGo’s dark web search engine may index pages on the dark web, but you’ll need to open it with Tor Browser.
- While Tor is the most common method for accessing the dark web, I2P and Hyphanet offer alternative options for secure and private browsing.
- Edward Snowden used the Tor global network on a regular basis.
- The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more.
Real Risks And How To Avoid Them
Always exercise extreme caution when using publicly posted onion URLs. There are no hidden terms or conditions—just contact support within 30 days if you decide NordVPN isn’t right for you and you’ll get a full refund. Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. All your traffic is automatically routed through the Tor Network. The easiest way to access Tor is through a special browser known as the Tor Browser. The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous.
A reliable free VPN for the dark web hides your activities by encrypting your internet connection and changing your IP address to hide your real location. It encrypts your connection, hides your IP address, providing protection when accessing the dark web. It aims to preserve your privacy and anonymity by forcing all internet connections through the Tor network and leaves no trace on the machine unless explicitly asked. It also hides your IP address and browsing data from any malicious Tor volunteers.
What’s The Difference Between Tor And VPN?
Once connected, the server will route and encrypt all of your internet traffic. It’s also useful if you’re a journalist, whistleblower, or activist that needs to share sensitive data with their sources, or if you’re an undercover agent. The Tor browser also lets you access dark web sites, which are not available on the clearnet.
The users of the dark web are typically aiming to block governments from snooping on them. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones.
Internet providers and websites can detect when Tor is being used because Tor node IPs are public. No standard web browsers can be used to access dark web content. Tor is a network of volunteer relays through which the user’s internet connection is routed. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content. As well as attracting cybercriminals who use the anonymity it provides to offer hacking and phishing services, the dark web is awash with illicit forums, malware, and other potentially dangerous content. All v3 .onion addresses (the current standard) are 56 characters long and end with “d” to denote the URL version in use.
There are both free and paid VPN services, but if you’re planning on accessing the dark web, you’re going to want to opt for a high-quality paid VPN that offers you plenty of protection. Now when it comes to the technical safety precautions that users should take when accessing the dark web, choosing and deploying a VPN is a critical first step. This process, though, can often involve accessing the dark web for research into the most current malware on the market.
As a result, “The quality of search varies widely, and a lot of material is outdated.” “Sites are constantly changing addresses to avoid DDoS, which makes for a very dynamic environment,” he said. The anonymous nature of the Tor network also makes it especially vulnerable to DDoS, said Keeper’s Tiquet. In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers.
These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Last but not least, we here at Pixel Privacy never condone illegal activity. If you decide to enter the dark web, always make sure to take all the necessary online privacy precautions.
I recommend reading up on your local laws to make sure accessing the dark web is legal where you live. Different factors can cause issues, including software compatibility, network settings, and server errors. However, all free VPNs have limitations, such as speed and data caps or small server networks. Tails is better suited for users looking for quick, easy access to the dark web with minimal setup. Whonix is particularly suited for users who are concerned with security and wish to operate in a controlled environment. That undermines Avira’s unlimited devices feature — with such little data, you won’t get much Tor browsing done before you eat up your allowance.
The browser uses a unique security system, which the United States Navy originally developed to protect the government’s intelligence communications. Suffice it to say that your Internet Service Provider (ISP) can detect when you’re using the Tor Browser, which can make you the target of increased surveillance by both the ISP and the government. Other users appreciate the browser as it allows them to circumvent censorship.



