Each network has its strengths, drawbacks, and intended use cases. The concept of a decentralized web, championed by technologies like IPFS (InterPlanetary File System), focuses on distributing content across multiple nodes rather than relying on centralized servers. I2P is an anonymous overlay network designed primarily for peer-to-peer applications. While Tor is the most well-known option, it’s not the only one. Exploring the Dark Web introduces risks that extend beyond network-level tracking.
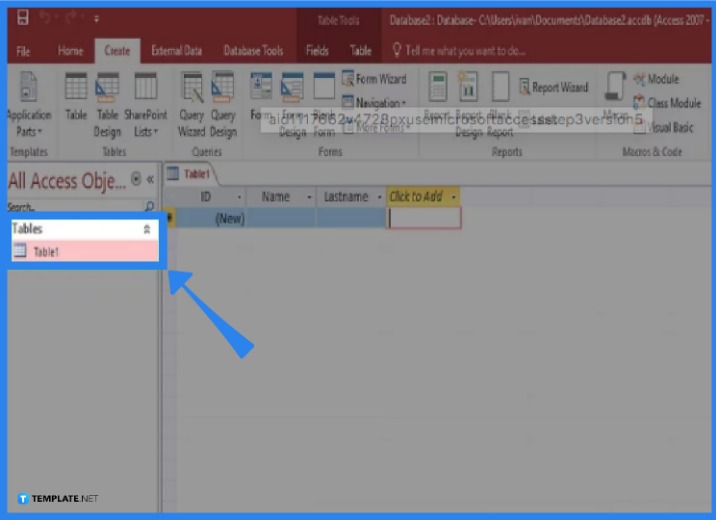
Step 3: Connect To The Tor Network
Using a reputable Virtual Private Network (VPN) or a secure proxy can help mask your IP address and encrypt your traffic before it even reaches the Tor entry node. Before you embark on your journey into the Dark Web, it’s crucial to establish a secure foundation. The “Dark Web” often conjures up images of hidden marketplaces, illicit trades, and shadowy figures lurking in the digital underworld. Nevertheless, it is vital to do not forget that the darkish internet is a continuously evolving and harmful place.
The Best Dark Web Search Engines In 2025
Now when it comes to the technical safety precautions that users should take when accessing the dark web, choosing and deploying a VPN is a critical first step. This process, though, can often involve accessing the dark web for research into the most current malware on the market. While there is a lot of criminal activity on the dark web, there’s nothing actually illegal about accessing the dark web.
- Instead, Tor uses a random set of encrypted servers known as nodes to keep users and sites anonymous.
- That means that even if an ISP is monitoring all of the known Tor relays, they may not be able to block all of the obfuscated bridges.
- By traditional websites, we mean websites with domains like .com, .org, .gov, etc., and easy-to-remember names, like google.com.
- The dark web is a small subset of the deep web comprising purely non-indexed websites and services.
- Tor shares similarities with VPNs and proxy servers — all of these tools allow anonymous browsing.
Marketplaces
For this reason, users should be cautious when using their browsers. There are plenty of harmless reasons sites stay out of sight, and they won’t put you or your computer at risk. The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet. If you already understand the fundamentals and want to get straight to the safety instructions, you can jump directly to our step-by-step guide on browsing the dark web covered later. The dark web and deep web host both legitimate privacy tools and illegal activities. But the question is, how can you access it safely and anonymously (of course, for legitimate reasons)?
That’s why it’s never a good idea to burn Tails on DVD. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails. Still, if you’re really itching to purchase a new phone or God knows whatever, I would advise you to stick with Bitcoins or your favorite crypto coin. Just click on the onion icon and choose Security Settings. Tor has an in-build slider which lets you adjust the level of security.
Using Tor Browser: The Final Step To Get On The Dark Web
Successfully navigating this hidden world requires preparation, vigilance, and a thorough understanding of both the technical and ethical challenges at play. The Dark Web remains a shrouded corner of the internet—an enigmatic space where privacy, free speech, criminality, and censorship resistance intersect. Remember that information security is an ongoing journey—regularly updating your knowledge and tools is key to making the most of the Dark Web’s privacy features while minimizing your exposure to its inherent risks.
How To Find The Best Midjourney Alternative In 2024: A Guide To AI Anime Generators
At a basic level, this tool and those like it route internet traffic through a series of servers, making it difficult to trace users’ identities or locations. The dark web is that part of the internet that is not accessible using traditional web browsers and search engines. A VPN will encrypt your internet traffic so when you access the Dark Web, it will not be possible for anyone to track your activities easily. If you’re worried about privacy and online tracking, there are easier ways to take steps to protect your data. If you’re particularly keen on maintaining anonymity, The Tor Project includes a number of warnings about what not to do when browsing the dark web.
- You can access many other sites via the Tor browser, and your requests will be routed through multiple servers to avoid monitoring.
- If you encounter this content label online, report it to the authorities immediately.
- Accessing the dark web isn’t like surfing the web everywhere else online.
- By using Tor Browser, individuals can navigate websites on the dark web that are not accessible through regular browsers.
- When you’re ready, hit the Close button and you’re all set.
Step 2: Download And Install Tor Browser
DarkWeb “marketplaces” guarantee confidentiality and anti-surveillance for your online purchases that you simply won’t find on any other websites. You will no doubt be surprised to learn that the Darknet hosts many websites similar to those you will find on the surface web (the visible/common internet we use). Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble. Not all dark web services are genuine, and many scam “.onion” sites offer downloads infected with backdoors and Trojan horses. Some websites monitor and analyze the dark web for threat intelligence.
VPNs, proxies, and alternative privacy-focused networks like I2P and Freenet also offer unique advantages. When considering anonymous browsing, Tor isn’t the only option available. Adhering to these methods will help you safely locate legitimate resources while minimizing exposure to potentially dangerous or fraudulent sites on the Dark Web. By following these straightforward steps, you significantly reduce the risk of exposure, protect your digital identity, and ensure a secure and anonymous browsing experience on the Dark Web.
Is The Tor Browser Secure?
Go to the directory where you saved the downloaded Tor Browser installation file. When the final layer of the “onion” is reached and decrypted, the message arrives at its destination. Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination.
How To Access The Dark Web Safely: A 2025 Beginner’s Guide
It’s important to note that Tor Browser may run slower than traditional browsers due to the encryption and multiple relays used to route your internet traffic. Using Tor Browser, individuals can browse the internet with a higher level of privacy and anonymity. Engaging in illegal activities can lead to severe consequences, and exposing personal information or engaging with malicious individuals can compromise your privacy and security. It uses technology like onion routing to hide users’ identities and encrypt their communications. We will discuss the setup procedure, ensuring security and anonymity, and offer tips for navigating the dark web safely.
Major Risks And Downsides
Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. The experience is reminiscent of searching the web in the late 1990s. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Estimates place the size of the deep web at between 96% and 99% of the internet.
There are numerous search engines for .onion websites. The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software (such as the Tor Browser), configurations, and authorization to access. The dark web (often referred to as the “darknet,” “black web” or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting. The Tor Browser (“The Onion Router”) is a product of the Tor Project, which was founded on the belief that “internet users should have private access to an uncensored web.” The dark web hosts a variety of content, including anonymous forums, marketplaces selling illegal goods (like drugs and weapons), hacking services, and information stolen in data breaches.
I’ve put together detailed guides on how to access the dark web safely on both Android and iOS. The editorial team did not participate in the creation of this guide. If you manage not to expose your private information and avoid illicit activities, you can be sure everything will be okay. Stick to tried-and-tested sites and do your best to avoid scams. Above all, it’s vital to go on the dark web carefully and sensibly. This internet space can be dangerous, but you can safely get on it by using a VPN and then connecting to Tor.
In this way, your browsing experience is made as anonymous as possible – if someone was ‘watching’ you, so to speak, all they’d be able to see is that you’re using Tor. With dangers like this in mind, it’s even more important to stay safe when surfing the Dark Web than any other part of the internet. Stolen information from data breaches, drugs, guns, malware and various other illegal items can be bought there.



