They require access to a specific VPN service and credentials before they can be viewed. Payment for these services is generally made using difficult-to-trace digital currency, such as Bitcoin. Securing this data prevents it from being compromised and possibly showing up for sale on the dark web.
Deep Web Vs Dark Web: What’s The Difference?
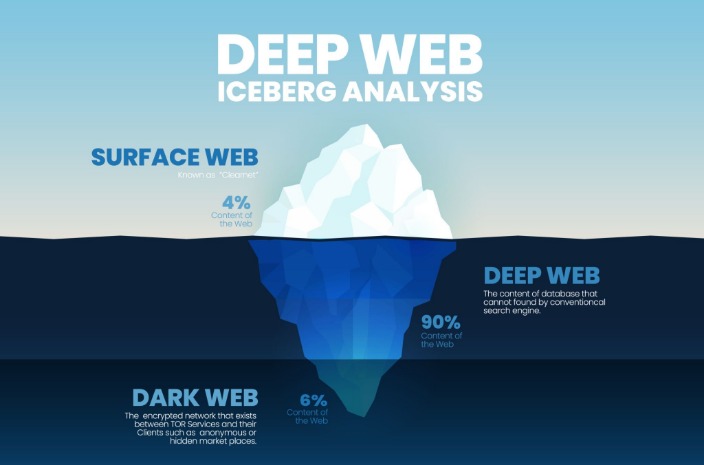
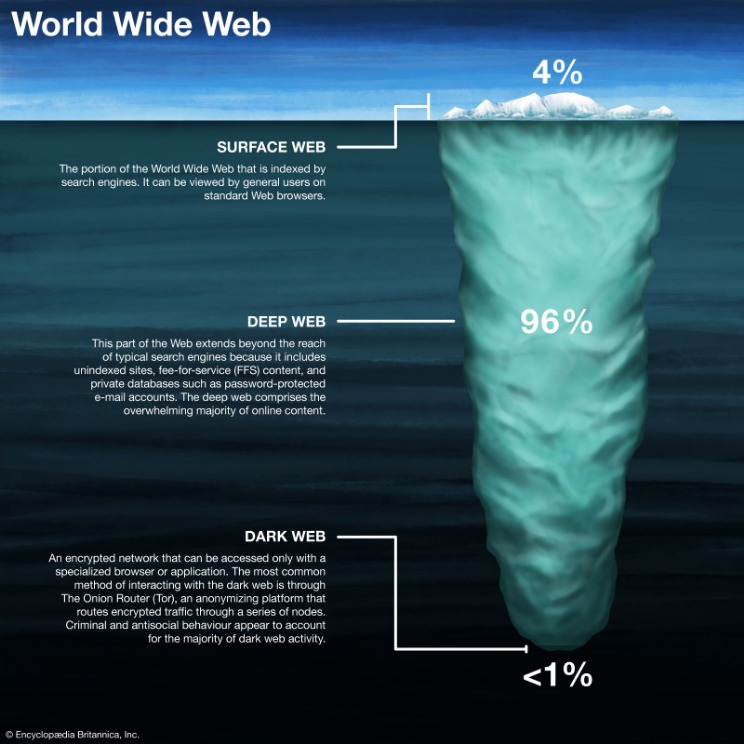
However, beyond what these tools reveal lies a vast, hidden part of the internet known as the Deep Web. Most people are familiar with search engines like Google or Bing. As people become more educated about how the internet works, they can make informed choices about their privacy, security, and digital identity. Artificial intelligence will play a growing role in mining hidden data for insights—provided that privacy is respected. These questions are especially urgent in the age of big data, where companies collect and analyze vast quantities of information about users. Military networks and cybersecurity operations are perhaps the most tightly guarded parts of the Deep Web, ensuring that sensitive national secrets remain secure.
Deep Web Guide: Getting There & How It Differs From The Dark Web
Many of these Reddits have rules prohibiting linking to illegal sites and services, so you likely won’t find anything illegal there. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. Obviously, since these websites don’t show up in the Google search engine, it can be a relatively hard task to find them. But, if you are planning to do more than just browse Tor sites and, for example, you plan to purchase goods via the Tor network (for your own good, stick to the legal stuff), it’s important to take some extra precautions.

However, note that the site only uses non-sensitive and public data for the metrics. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. For example, the BBC website is not accessible in such countries. After all, it enables users to connect and communicate with each other from around the world. The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
Government Monitoring
Whether you’re browsing the surface web, the deep web or the dark web, Hancock said the same advice applies — proceed with caution. Governing bodies have many ways of tracking down users who engage in criminal activity, even on the dark web. “Taking down the deep web would require coordination from several countries and many would argue that is a violation of rights.” Additionally, the technology for onion routing was actually developed by the U.S. The dark web’s anonymity makes it a safe space for whistleblowers, which also makes it a valuable source of information for the government.
Deep Web Search Engines
The deep web and the dark web have been conflated in public discourse. (If Google can find it, then it’s on the surface web, which makes up about 0.03% of the Internet.) When you think of the deep web, what comes to mind? I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. Great life advice, but it’s even more valuable where the darknet is concerned.
Mullvad VPN
For example, the Social Science Research Network has over 1 million academic papers uploaded. Sometimes, people also hide content from the surface web to protect copyright. You don’t want to wake up one morning to find that the credit card details you stored on a Fintech company’s website are now on the first page of Google. This is necessary due to the kinds of information that you’ll find on the deep web. That means you decide whether you want any search engine bot to crawl your webpage. For a web page to be on the surface of the web, such as on Google search engine result pages, a web crawler must first crawl and index it.
- Many sites use this file to intentionally exclude sensitive or irrelevant content from search engine results.
- This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
- And media portray the deep web as illegal for two primary reasons.
- Governments, businesses, and individuals rely on it for secure data storage.
- However, they refer to different parts of the internet with distinct characteristics and purposes.
Regular browsers access much of the deep web, especially sites behind logins. Yes, the deep web is safe and legal when accessing legitimate resources like your bank or email. Besides the illegal activities on the Dark Web, political dissidents and privacy advocates also use it for anonymity. Many dark web sites deploy tools that prevent bots and web crawlers from accessing the site. For example, to access the popular dark web forum CryptBB, you must know the exact onion link; conducting a web search for the forum will not turn up anything useful.
As when visiting ordinary websites, stay alert to security risks on onion sites. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. The deep web is the part of the web that can’t be reached through typical search engines and often requires getting through additional layers of encryption to access.
Once you have these deep web sites links, simply copy paste any one of these links on Tor browser, and you should be on the deep web site soon enough, station darkweb has arrived! I’m sure you know by now that the interesting stuff, or what you actually wish to access is the “Dark web” and not the deep web. So hey, we’ve beaten around the bush quite a bit, let’s finally get you what you came here for, here’s how to access the deep web. That’s so because it’s already an illegal arena, so you can’t exactly go to the authorities about it.

Best Dark Web Sites 2025 – Detailed List
However, you cannot simply browse to sites on the dark web — you have to take steps to ensure privacy first. Organizations constantly face the risk of data breaches, but the existence of the dark web amplifies this risk. Though the dark web may not be the monster it’s often made out to be, its very existence poses a risk to the rest of the World Wide Web.
When it comes to dark web safety, the deep web dangers are very different from dark web dangers. The dark web, however, is a very concealed portion of the deep web that few will ever interact with or even see. Significantly smaller than the tiny surface web, the dark web is considered a part of the deep web. At the dark end of the web, you’ll find the more hazardous content and activity. Venturing further into the deep web does bring a bit more danger to the light.
While both spaces can host both legal and illicit activities, the Deep Web typically serves as a haven for legitimate endeavors, contrasting sharply with the Dark Web’s notoriety for fostering illegal activities. The integration of web content into the Surface Web involves the deployment of web crawlers by search engines like Google, Yahoo, and Bing. Its content remains beyond reach due to either partial indexing by search engines or the imposition of password protection measures.
It will offer you an additional layer of encryption to access the deep parts of the internet. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. It has onion links you cannot access with regular browsers like Chrome, Firefox, Edge, or Safari.
Tor encrypts your traffic through multiple relay nodes, but it’s important to understand that this encryption is removed at the exit node before reaching its final destination. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened. This runs the gamut from illegal substances to personal information, credit card details, child sexual abuse material and, allegedly, assassination contracts. This is when it takes a search query from the user, finds the most relevant results in the index, and then serves the resulting web pages back to the user. The terms “deep web” and “dark web” are commonly used interchangeably. If your website is only accessible through the deep net, tracking down the physical location of your servers is much harder than it would be for a regular website.



