The service retains no copies of any data that passes through a ProtonMail account. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. The software requires two-factor authentication to receive what’s been uploaded by the whistleblower and allows two-way communication between the anonymous contact and the media outlet.
How The Deep Web Is Different From Traditional Internet
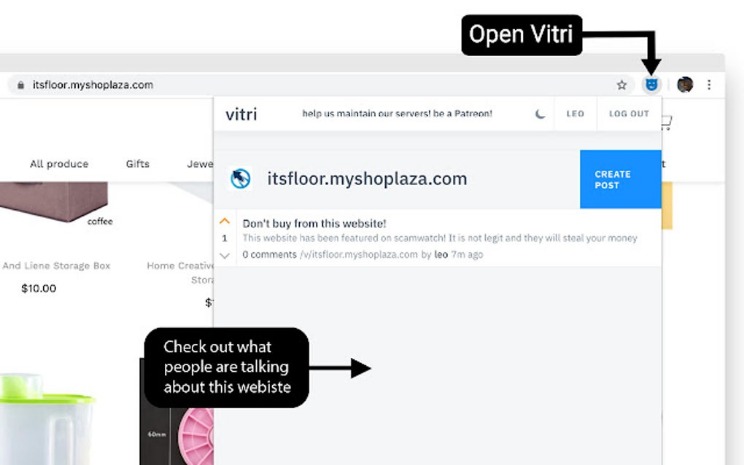
It’s a place where you’ll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. Back when reliable dark web search engines were limited, the Hidden Wiki served as a trusted compass for exploring the hidden layers of the internet. Hovering isn’t possible on Tor like in normal browsers, so it’s crucial to verify links through directories like dark.fail or onion.live before you trust them. The dark web may offer access to valuable resources, but it’s also filled with traps, especially fake dark web sites designed to scam or harm unsuspecting users. Unlike surface engines, Haystak offers deep crawling and metadata previews to help users navigate through hidden content. It categorizes links by function — markets, forums, search engines, privacy tools — and also includes uptime indicators.
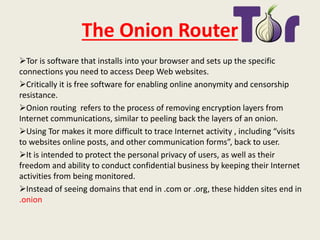
Why Is Tor So Slow?
It filters out illegal and scammy content while indexing only verified .onion links. In an age of surveillance and data leaks, these hidden networks still offer something the surface web often can’t — freedom and anonymity. For users looking to preserve their privacy, knowing how to find real dark web links and access dark web sites that are safe in 2025 is essential. These .onion sites are hosted on the Tor network, which encrypts traffic and routes it through multiple nodes, making it extremely difficult to trace. These sites aren’t accessible via standard web browsers or search engines.
✅Final Thoughts – Stick To Known, Safe Directories
Switching to ProtonMail’s .onion site does two key things for you. You get two options for searching, including ‘match any words’ and ‘match all words.’ Every time you log in, you’re risking scams, having your own data stolen, or facing serious criminal charges. From fake IDs and stolen credit card info to drugs and hacking tools, users buy and sell everything, all while hiding their identities. Here, under the cover of Tor and cryptocurrency, people buy and sell pretty much anything illegal you can imagine. If you’ve heard of one dark web marketplace, there’s a good chance it’s Awazon.
PRIVACY ALERT: Websites You Visit Can Find Out Who You Are
The BBC Tor mirror is a secure version of the official BBC News website that runs on the Tor network. Moreover, the darknet search engine sends your search queries via HTTPS POST to prevent the servers from logging your data. ProtonMail’s onion site offers secure communications with end-to-end encryption.
Deep Web Users Of Reddit, What Are Your Worst Or Scariest Experiences You’ve Had While Browsing?
- It’s an interesting resource that translates Tor internet traffic levels into easy-to-digest stats.
- These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes.
- Any veterans able to give advice on setup, security and how to spot scams when buying from sellers on there.
- We strongly recommend shielding yourself with a VPN before you access the dark web.
- Although there is some crossover, the list of sites on OnionLinks is broadly different from those on The Hidden Wiki.
- Fortunately, you can upgrade to the premium version and avoid that altogether while accessing advanced searches and results from historical onion sites.
ProPublica is independent, so you’ll find trustworthy news reports on topics ranging from corruption to inequality and environmental issues. Accessing ProPublica via the Tor Browser gives users an added layer of privacy and lets them bypass restrictive government censorship. However, Ahmia doesn’t have a large developer supporting it, so it’s been the target of scams or cyberattacks in the past. You’ll get unbiased, organic search results without getting any of your browsing behavior logged. You can access DuckDuckGo on the surface web, but a Tor version is also available. It doesn’t track browsing habits or personal data and won’t expose a user’s identity or location.
Verified Social Channels And News Sites
Built with privacy in mind, Ahmia lets users explore dark web sites without exposing them to risky or harmful pages. Ahmia is one of the most respected dark web search engines available today. Remember to use the Tor Browser to access these, and always type the dotonion address carefully to avoid fakes. Many directories are outdated or cloned, while others include malicious .onion addresses.
Verified directories, anonymity tools, and cautious clicking make all the difference. Many phishing sites imitate trusted platforms like the Hidden Wiki to trick users. This added layer of anonymity is what sets these links apart and is the reason so many seek out dark web links in the first place. Dark web sites use a different kind of domain — the .onion extension — which doesn’t work on regular browsers. The dark web, however, is a small, intentionally hidden part of the deep web that requires special tools like the Tor Browser to access.
The anonymized browser won’t protect you if you do such things online, and you keep wondering if it is illegal to visit dark web sites. In fact, it has many benefits, like better privacy and access to undetectable content and services. This is a community space where users post reviews, discuss new markets, share onion links, and exchange information. Though it’s no longer active, it set the benchmark for future .onion directories. Although the Hidden Wiki is well-known, it’s unreliable since it lists some illegal or unsafe links.
This sequence offers less anonymity because your real IP address is still partially exposed along the Tor path. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. It’s still illegal to commit crimes while connected to Tor, regardless of whether or not you think you’ll be caught.
- However, data is required for understanding, monitoring, and improving the network.
- That’s why we took the guessing work out of it for you, and made this list of the best dark web sites you should check out.
- I know how to use Tor and DuckDuckGo, so just send some good links.
- Thanks to its long history, technically skilled community, and organized structure, BHF has become a significant player in the Russian cyber underground.
🔗 Top 12 Dark Web Sites And Verified Onion Links (

So, you should still use strong passwords and two-factor authentication (2FA) to protect your accounts even when using Proton Mail on Tor. Second, it layers ProtonMail’s own end-to-end encryption with the full anonymity of Tor. First, it bypasses censorship, giving you access where the standard site is blocked.

It works by sending internet traffic through volunteer-operated nodes all over the world. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. Onion links have no regular domain names registered under the domain name registry.
Nevertheless, the dark web is home to certain disturbing and illegal content you’ll never find on the surface web. As long as you are not looking for anything illegal in the real world, it’s perfectly legitimate to use the dark web to find whatever you need. For the record, there are more scam sites for every genuine one, and it’s good to have a discussion forum about this. It offers a Reddit-like interface, where you can learn everything you need to know about darknet websites and spotting the real from the scammers.
If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. This is because law enforcement often actively monitors these sites. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. The threat can extend to your entire network of devices connected to the internet. For example, China uses the Great Firewall to block access to Western sites.
Pastebins are text sharing services, useful for sending and sharing large snippets of code or text. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide. Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. Why would one of the largest organizations known for its invasiveness and controversial clear-name policy have a .onion address?

Given the anonymous nature of the platform, it hosts a mix of legitimate inquiries and discussions alongside more contentious or illicit content, reflecting the diverse interests and intents of its user base. The site also serves as a resource for information and advice on navigating the dark web, including safety tips, recommendations for secure communication, and discussions about the ethical and legal implications of dark web activities. The anonymity offered by Hidden Answers fosters a community where open, honest dialogue can flourish, covering subjects that might be taboo or heavily moderated on conventional platforms. Hidden Answers is an anonymous question-and-answer platform located within the dark web, serving as a unique confluence of curiosity, information exchange, and anonymity. The platform utilizes various methods to bypass paywalls, including using donated institutional login credentials and other access mechanisms.
But unlike other wallets, you don’t have to worry about your personal information being leaked since it’s hosted on the Tor network. However, dark web users have relied on Bitcoin transactions for over a decade, as they allow people to make payments while staying completely anonymous. You can use Facebook’s services without exposing yourself to the company’s privacy-eroding tentacles. Make sure you’re smart about which dark web links you click on.
Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. It provides an .onion URL and an interface for you to manage your Tor site easily. Impreza Hosting is a service that helps you host a site on the Tor network. ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it.



