Premium users gain access to private Telegram channels, including an exclusive leak channel not available to regular members. When BreachForums shut down, many threat actors were left searching for a new place to carry on their operations. For cybersecurity professionals, it’s a critical source for spotting emerging threats, tracking criminal group activities, and understanding trends in the digital black market. While there’s significant discussion about privacy and legitimate cybersecurity, it’s also undeniably a space where illicit commerce is promoted and organized. It operates entirely within the Tor network, which enhances user anonymity. It features separate sections for malware, tools, exploits, and of course, everything related to leaked databases.
Dark Web Marketplaces

Also, people share reputable dark web links on encrypted apps like Telegram or Keybase. However, you’ll need to use specific keywords when searching on these dark web search engines. Other alternatives include NotEvil, Ahmia, and Torch, which list .onion links.
Role Of Dark Web Monitoring And Threat Intelligence
- The dark web version allows users to access these services anonymously.
- This directory focuses on providing users with verified, frequently updated links to a broad range of dark web services, including marketplaces, forums, and whistleblower platforms.
- When you buy or sell illegal goods online, you are not hidden from law enforcement, Europol’s director emphasized after a Dream Market bust.
- The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit.
- The reviews published on Wizcase are believed to be accurate as of the date of each article, and written according to our strict reviewing standards that prioritize professional and thorough examination by the reviewer, taking into account the technical capabilities and qualities of the product together with its commercial value for users.
- Second, it layers ProtonMail’s own end-to-end encryption with the full anonymity of Tor.
Hidden Wiki was originally the name of a .onion hidden service on the Tor network, hosting a directory for links to websites on the Tor dark web. Dark web search engines help users discover hidden .onion content that isn’t indexed by traditional search tools. You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. Instead, the addresses are self-authenticating, and the network relies on a distributed system to locate and connect users to these hidden services, adding another layer to the onion’s anonymity.

A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. However, no matter how much you try to stick to legal websites, you can still land on illegal or highly disturbing content.
onion Links
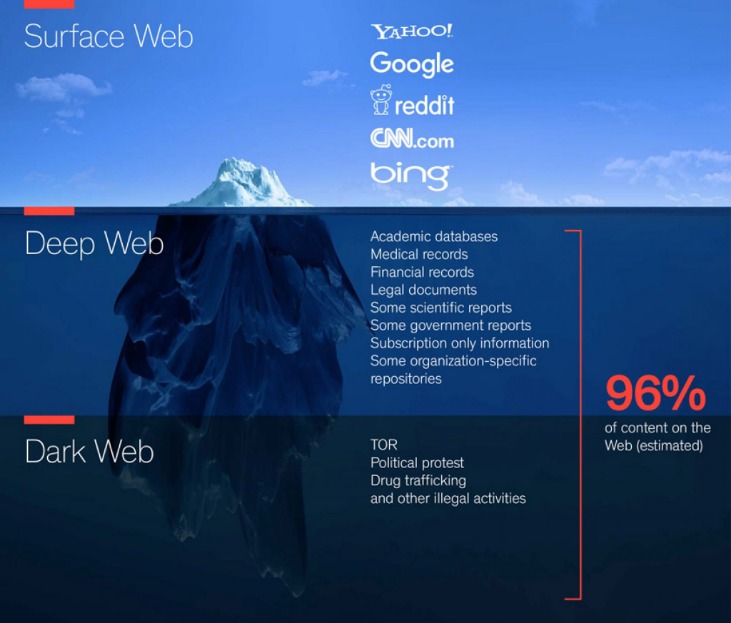
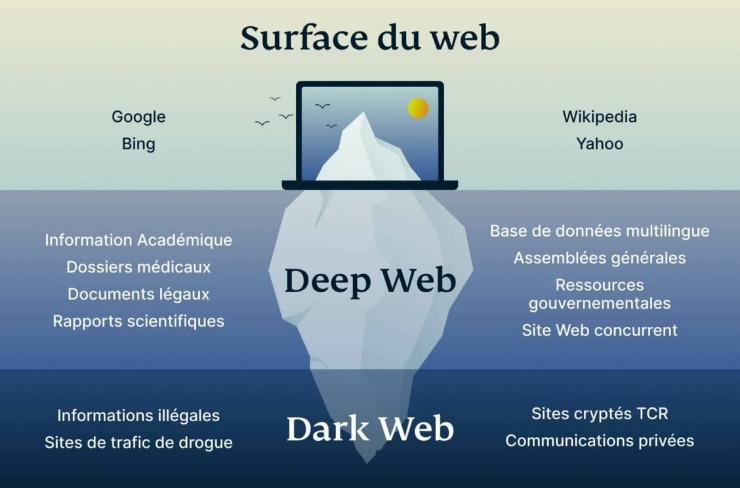
Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. With the onion browser, you can access ordinary HTTPS websites on the web. You will find all the necessary .onion links to access any content or service on the dark web. Unlike other search engines, it does not collect or share web activities and personal data of users. You will need the Tor browser to access these links and the other (hidden) internet, the dark web.
Vulnerability In Windows Server 2025 DMSA Exposes Active Directory
No, you cannot reliably access the Hidden Wiki without the Tor Browser because its URLs use the .onion domain, which is only accessible via the Tor network. Browsing onion sites safely requires using the Tor Browser, which anonymizes your internet traffic. However, users should still exercise caution as no directory is entirely immune to malicious links. Dark.fail also emphasizes user security by offering warnings about phishing sites and scam links. First, rely on community-vetted sources and updated link lists from trusted forums like Dread or The Hub, where users report scams and share verified onion addresses.
Risks Of Using Dark Web Search Engines
Although they are sometimes used interchangeably, they refer to distinct parts of the internet with their own characteristics and purposes. Two terms often mentioned when discussing these hidden areas are the deep web and dark web. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web.
Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. It allows you to search for images, maps, files, videos, social media posts, and more. SearX is a metasearch engine that you can use on the clear web and dark web. Visiting the links from specific questions may be a bit safer. However, that part of the internet is unfiltered, so you might encounter unpleasant conversations. Its mission of open access is debated within academic and publishing communities.
Can Google Take You To The Dark Web?
It operates on encrypted networks, primarily Tor, using .onion URLs to ensure user anonymity. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously.
Hosting & Development: Daniel’s Hosting, OnionShare, Tor Project Onion
If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. Just as you explore hidden corners of the internet, you need to secure your data on the go. For example, whistleblower platforms such as SecureDrop use onion websites to securely transmit confidential information to journalists without revealing the source’s identity. Onion websites are therefore caught between the legitimate desire for privacy and the challenges that arise from their misuse.The dark web, accessible through onion websites, is a double-edged sword. This entire process ensures that the Tor network itself does not need a central directory of .onion sites. However, this same anonymity also makes onion websites a breeding ground for illicit activities.
Haystak offers a more advanced experience, including metadata previews and paid access to deep datasets. Below are the main categories of dark web sites in 2025, along with examples of what users typically find in each. While many newcomers assume it’s all about illegal marketplaces, the reality is far more complex. Many phishing pages and malware traps are hidden behind .onion URLs that look almost identical to the real thing.
These forums are frequently accessed via the top 10 dark web search engines, serving as essential resources for information and networking. WormWeb is a user-friendly search engine built specifically for the dark web, providing quick and easy access to .onion websites. It delivers an uncensored search experience, granting users access to a diverse array of information while effectively excluding illegal content. You can also use security tools with AI-powered scam detection capabilities to identify and block suspicious links and websites in real-time when browsing the dark web. While some users seek privacy, the ease of trading stolen data and illegal services remains a major cybersecurity concern.
In other words, it’s the dark web’s version of ScienceDirect. The first website on our list is, allegedly, the largest repositories of scientific papers on the dark web. With these in mind, let’s take a closer look at the dark web sites rundown. Hackers, both white- and black-hat, can also be found scouring the depths of the dark web for things like malicious code, special hacking tools, victims, and more.



