Most estimates show that the deep web is between 400 and 550 times bigger than the surface web. There are no hidden terms—just contact support within 30 days if you decide NordVPN isn’t right for you, and you’ll get a full refund. You can use the VPN rated #1 with no restrictions for a month—great if you need time to test if it’s the right VPN for you. In addition, studies have revealed that many VPNs lack reliable security.
How To Safely Navigate The Dark Web

TorLinks maintains one of the most reliable directories of verified .onion sites. Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams. Researchers have been exploring how the deep web can be crawled in an automatic fashion, including content that can be accessed only by special software such as Tor.
Understanding The Deep Web, Dark Web, And Darknet (2025 Guide)
Conventional hosting with access controls Valid credentials or authorized access Information protection, authentication-restricted access Privacy, censorship circumvention, and often illicit activities
Are There Legitimate Uses For The Dark Web?
If your information surfaces in these murky depths, there’s very little you can do – but knowing the risks involved is a first step toward defence. To counter this, dark web monitoring has become essential to detect these threats and safeguard digital privacy. From information security threats like identity theft and malware to scams and surveillance, navigating the dark web without caution can lead to real dangers. It is used to provide access to a specific group of people. These data are sensitive and private, so kept out of reach. Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands.
The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites. Torch is one of the oldest dark web search engines, and it’s generally considered one of the safest. It has indexed more than 1.5 billion pages from over 260,000 .onion websites, so you’ll easily be able to find what you’re looking for. DuckDuckGo is a search engine available on the Tor network that lets you browse the surface and dark web. Ahmia is a search engine for .onion sites — you search for a keyword and Ahmia retrieves relevant results.
- The dark web, a subset of the deep web, cannot be accessed with a regular browser.
- Just as you need the right tools to access the dark web, you also need the right protections to be able to stay safe on it.
- An easy way to find content on the dark web is to receive a link from someone who already knows about it.
- But it is not all bad; the dark web’s anonymity also allows well-meaning individuals, such as whistleblowers
- It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself.
Is It Safe To Browse The Deep Web?
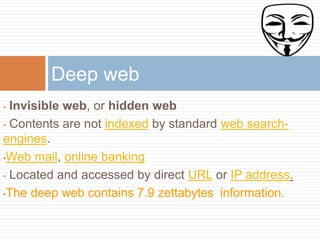
The contents of the deep web range from pages that were not indexed by search engines, paywalled sites, private databases and the dark web. Over 96% of the internet lies beneath the surface web, hidden from regular search engines like Google or Bing. While the Tor network was not created for illegal activities, as it’s harder to trace websites to their physical location, cybercriminals have also adopted it to host their websites.
OnionName — Buy Readable Onion Domains
Nearly all dark web commerce sites conduct transactions in bitcoin or some variant, but that doesn’t mean it’s safe to do business there. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims.
Many dark web sites deploy tools that prevent bots and web crawlers from accessing the site. These networks use the infrastructure of the Internet for communications, but access to them is restricted. These include peer-to-peer and privacy-focused networks and can only be accessed using special tools like the TOR browser.
Ready To Revolutionize Your Security Operations?
Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. If you want to buy something on the dark web, it’s a best practice to create a fake identity. Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users). MacOS users will need to drag and drop the Tor Browser icon to the Applications folder.
Quick Links
In an era of mass surveillance and data harvesting, some users simply want to reclaim their privacy and browse the internet without being tracked. The anonymity of the dark web unfortunately attracts a wide range of illegal activities. The deep web refers to any part of the internet that is not indexed by search engines. The dark web is a part of the internet that isn’t indexed by search engines like Google or Bing.
- Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users).
- It has a feature called CoinJoin that combines multiple coins from different users into a single transaction.
- Obviously not all Tor users, but you never know whether someone might be looking into you.
- What’s more, they can also sell you personal information on the dark web as your personal data has a monetary value on the dark web.
- Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling.
They asked for our personal information in exchange for access to the forum. Phishing is when someone contacts you pretending to be someone else to gain access to your personal information, which often results in identity theft. One key reason is the anonymity the dark web provides. Dark web URLs are often made of a random and long alphanumeric string, which makes them harder to verify than surface web URLs. As for how threat actors spread malware, they can use a variety of techniques. When browsing through Tor on the dark web, however, the suffix is .onion.
DeepPeep, Intute, Aleph Open Search, Deep Web Technologies, Scirus, and Ahmia.fi are a few search engines that have accessed the deep web. Bergman, in a paper on the deep web published in The Journal of Electronic Publishing, mentioned that Jill Ellsworth used the term Invisible Web in 1994 to refer to websites that were not registered with any search engine. While the deep web is a reference to any site that cannot be accessed by a traditional search engine, the dark web is a portion of the deep web that has been hidden intentionally and is inaccessible by standard browsers and methods.
Infamous examples of Dark Web sites include the Silk Road and its offspring, such as Dream Market. The visitor has to use the same encryption tool as the site and – crucially – know where to find the site, in order to type in the URL and visit. Some use similar services such as I2P, for example the Silk Road Reloaded.
These marketplaces are similar to that of eBay or Craigslist where users can interact with sellers and leave reviews about marketplace products. These markets have no protection for its users and can be closed down at any time by authorities. Silk Road was one of the first dark web marketplaces that emerged in 2011 and has allowed for the trading of illegal drugs, weapons and identity fraud resources. Commercial darknet markets mediate transactions for illegal goods and typically use Bitcoin as payment.



