
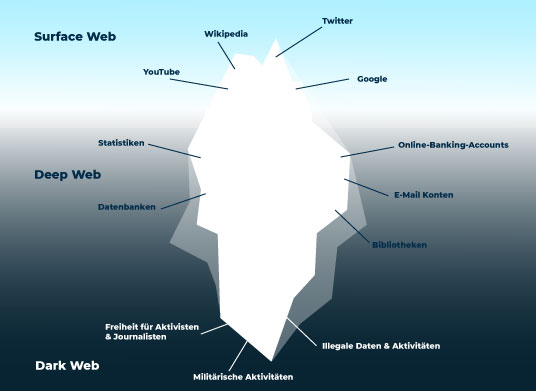
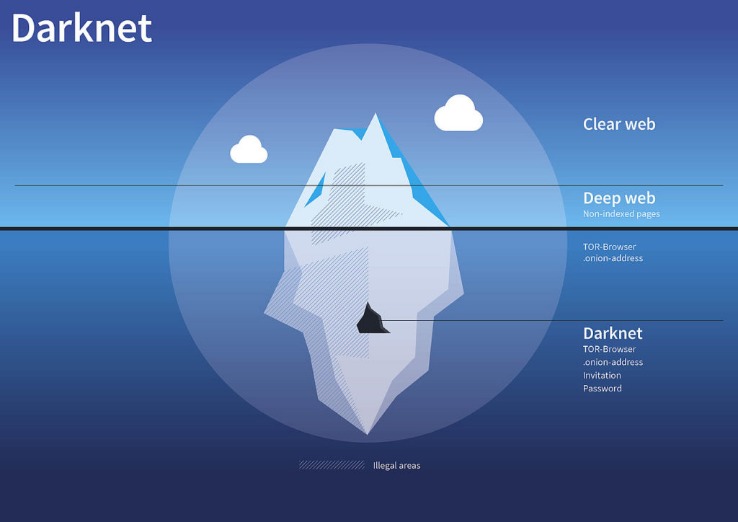
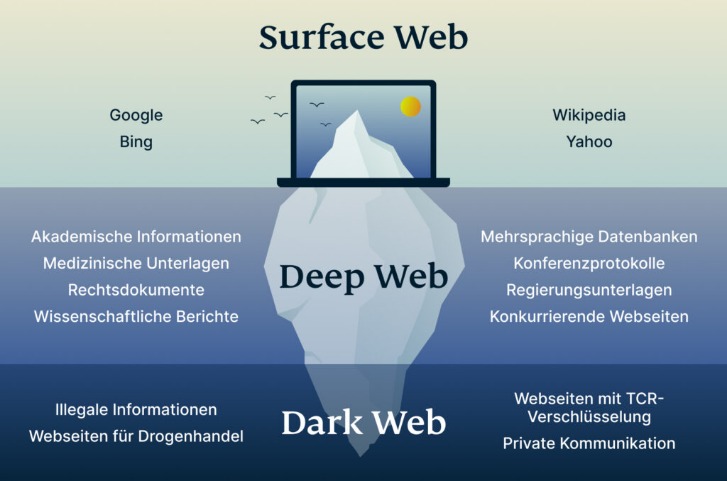
It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. This is the part of the internet known as the dark web, and it’s accessible via mainstream search engines such as Google. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online.
Hidden Answers
DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
What Is IPsec? The Definitive Guide For 2025
Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser. The Tor browser is designed to provide improved online anonymity and security. However, some Tor users do so to facilitate illegal online acts.
Arti 170 Released: Onion Service Restricted Discovery, Experimental HTTP Proxy, Relay Development, And More
DuckDuckGo is a privacy-centric search engine that focuses on user anonymity and data protection. The biggest difference is that the Tor website encrypts users’ internet traffic and anonymizes their connection. Also known as deep web sites, these pages typically have URLs ending in .onion and are only accessible through special software like the Tor Browser. You should keep in mind that the more restrictive security you select, the slower your connection becomes, and some websites may not load at all or have limited functionality. It gives you a way to experience the internet in a more private and protected way, as it uses the Tor network to route your traffic. Anyone concerned about user privacy, anonymity on the internet, and digital security should consider downloading the Tor Browser.

In “safer” mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won’t run automatically, you’ll have to click to play. There are different levels of security in the browser that are worth considering. If you’re having trouble connecting to the Tor network, try one of these. That’s the desktop edition, but there’s a version for Android and an unsupported onion browsing app for iOS. If someone visits two different sites that use the same tracking system, they’d normally be followed across both.
Vorm Web Search Engine
Not every visitor is a criminal, but this is where most cybercrimes begin. However, under the surface, they can provide total anonymity. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. Onion links have no regular domain names registered under the domain name registry.
You can’t search for .onion sites using Google. These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. Some of the websites to look out for on the dark web include mirrors of both the BBC and the ProPublica investigative journalism platforms, built to help inform people who are living in countries where the internet is heavily censored. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. However, there are plenty of legal and legitimate online activities that require privacy and anonymity.
- Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.
- Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
- The darknet markets are a hotbed for selling stolen personal information.
- When the Tor Browser is launched, you will be brought to a purple homepage with a search field for the DuckDuckGo search engine in the center of the screen.
- These search engines help users find marketplaces, forums, data leaks, whistleblower content, and more — all anonymously.
The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. The inherent anonymity of the place attracts scammers and thieves, but what do you expect when buying guns or drugs is your objective?
News, Media, And Other Information Organizations
These sites aren’t accessible via standard web browsers or search engines. However, there’s a chance you may run into illegal activity on all but the best onion sites. The dark web is just a part of the internet where users can communicate and browse privately, often beyond the reach of standard government monitoring. Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet. Malicious actors can prey on unsuspecting users without leaving much of a digital footprint on Tor, so it’s often just a matter of time before you run into one. ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network.
How To Use Tor, And Is It Safe To Access The Dark Web?
When your data is found on the dark web, it means that you’ve been compromised. You can use a dark web scan tool to tell if your data has landed on the dark web. It’s one of the largest darknet markets that launched in 2022 and trades sensitive financial credential transactions.
While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Many people see hacked information and stolen card data being sold on the dark web. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
Justice has acquired extensive content writing experience over the years. Justice Ekaeze is a freelance tech writer with experience working for specialized content agencies. Hence, protecting your online privacy goes far beyo…
Needless to say, we don’t condone any content forbidden by law. Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. Naturally, this makes the dark web a breeding ground for illegal activity.
The only difference is that it passes your traffic through random nodes before reaching the destination. In due course, the framework was remodeled and made public as a secure browser. Since the internet is open to everyone, there is no privacy. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe. If you’re seeing this message, access is restricted for regular browsers. Tor Browser 15.0a4 is now available from the Tor Browser download page and also from our distribution directory. When censorship strikes, Tor provides a lifeline to access information–a lifeline to a FREE INTERNET.
Explore Top Darknet Markets
Tor uses onion routing to encrypt and reroute web traffic through Tor’s onion network. Silk Road’s demise proved that even Tor hidden sites could be penetrated by good detective work, prompting many users to flee to successor markets. These hidden markets promise anonymity, but in practice, users often slip up. Dark web marketplaces are hidden online bazaars on Tor or similar networks where anonymous vendors sell illicit goods. Explore more Tor-related topics, including relays, onion services, metrics, and ways to contribute to the network. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content.
Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. Note that engaging with the content in any way is not only distressing but could also put you at legal risk. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark web sites offer malware as a tool for cyberattacks. Accessing blocked content can result in being placed on a watch list or imprisonment.
Tor Metrics highlights that about 22% of daily Tor users come from Russia, while the USA ranks second at 15%. This space for private free speech also carries the risk of exposing you to harmful content. Posts on controversial or even illegal topics are fair game, so the Tor website is a double-edged sword. Although Hidden Answers offers an outlet for anonymous dialogs, users should stay cautious while browsing. Hidden Answers is one of the biggest question-and-answer dark web sites. This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy.



