
Recently, Telegram has faced criticism for its lax content moderation policies (Mackintosh and Vernon, 2024; Chayka, 2024; Boot, 2024; iconLindsay Clark, 2024). One platform that has emerged as a new frontier for cybercrime is Telegram (Telegram Messenger LLP, 2023), a messaging service known for its encrypted communications. The project has been up for quite some time now according to its official page on X, and is a very reliable resource to browse through Telegram content. In my honest opinion, this is one of the most efficient and straightforward third-party search engines for Telegram, and that’s why I saved the best for the last! The interface is pretty simple and you do have to scroll down to get to the search results after pressing the “search” button.
Files detected as malicious were further examined using MITRE ATT&CK techniques (Palo Alto Networks, n. d.) to assess the severity of the threats, as depicted in Figure 7. We reported all malicious URLs to five popular anti-phishing blocklists (Google Safe Browsing, APWG eCrime, PhishTank, OpenPhish, and Microsoft SmartScreen) and reported the posts containing these URLs to Telegram.. Notably, 74% (2,854) of URLs flagged by VirusTotal had fewer than 10 detections, showing that most security vendors missed them.
How To Search For Videos On VK Without An Account

The platform’s efforts to combat CSAM and other illicit activities fall short, with insufficient action taken against offending content. These groups exploit the app’s private channels to disseminate propaganda and recruit members, operating with reduced scrutiny compared to more regulated platforms. The ease with which users can access these groups underscores the app’s function as a digital marketplace for illicit activities. We see many of the same threats on Illicit Telegram channels that we see on dedicated dark web markets and forums. According to the reports, perpetrators then disseminated stolen information through social media platforms, eventually putting it up for sale on the dark web forums.
Will Threat Actors Leave Telegram For Other Messaging Platforms?
In contrast, blackhat resource channels contributed only 87 phishing URLs, as users here tend to have higher technical knowledge and are more vigilant. With only 2 out of 42 channels removed, it appears that channels sharing exploit tools and hacking material receive the least scrutiny. Pirated software, like copyright media, is often easier to detect and report, and software companies frequently have robust mechanisms in place to identify and flag unauthorized content, which can then prompt swift action from Telegram. The removal rate for pirated software channels, though lower, indicates a focused effort by Telegram to curb unauthorized software distribution.
Best Free Courses posts stolen content from Udemy courses on its Telegram channel. While this channel might technically be safe as it only posts links, channel users might participate in crypto scams and fake offers of NFTs, putting you at risk. Narcotics Express is a closed Telegram group, meaning users must request access to view content. Dig a little deeper, and some of those chat groups and channels have users that want to scam you. Get notified about new channels and trending content But drug dealers can often be seen advertising their Telegram channels on those other sites to funnel people to that platform.
Breached Data
- Based on Telegram’s data, more than 14 million groups and channels have been blocked by the app in the first half of 2025 alone.
- The platform’s allure lies in its security features, while the broad range of criminal activities taking place within it underscores the ongoing challenges of surveillance and regulation.
- Waybien is a third-party custom search engine for Facebook, Discord, and WhatsApp, also supports Telegram.
- In 2024, Europol reported seizing more than 200 illicit Telegram channels tied to malware distribution and darknet fraud.
- We observed a significant increase in follower growth for the new channels, with a median of 43.8% of followers migrating within a week.
Other popular exploitation methods included instructions on setting up and managing botnets, methods for spreading malware, using crypters (a form of malware obfuscation, which will be further cited), and techniques for cashing out cryptocurrency, offering a comprehensive suite of tools for aspiring cybercriminals. In 5.7% of the cases, these demonstrations were complemented by text/images, including success stories and testimonials from users claiming to have benefited from the shared knowledge, serving as validation for the techniques. For instance, 15.9% of posts showcased successful phishing campaigns or detailed how to execute Distributed Denial of Service (DDoS) attacks, with a significant number (59) also providing the necessary toolkits. The majority of these tutorials were disseminated through YouTube links, demonstrating how to set up and use specific hacking tools, complete with visual walkthroughs.
The 2024 arrest of Telegram CEO Pavel Durov raised concerns among threat actors. Free, encrypted, and fairly anonymous, Telegram has been home to several criminal forums and marketplaces for years. To save some time and effort, consider using NordStellar — a cyber threat monitoring and threat exposure management solution. Protecting your business from online threats is a perpetual challenge. Leaked data reportedly included sensitive financial information about prominent figures and institutions. The agency, which manages pensions and insurance for millions, confirmed that hackers bypassed its security but did not identify those responsible.
Security Links
- Harmful content can include phishing scams that trick users into providing sensitive information, and malware that can infect and compromise the security of their devices.
- Many threat intelligence platforms now include Telegram feeds.
- We tracked the growth of followers across all CACs in our database over the study period, yielding insights into their growth patterns.
- It explores its features, the criminal activities facilitated on the platform, and the broader implications for security and regulation.
- However, no platform is completely immune to threats, and Telegram users should be aware of common threats that can potentially compromise their privacy and security.
Its approach to police requests to remove illegal content and pass on evidence is another criticism. Telegram told the BBC it does proactively search for illegal activity, including child sexual abuse, on its site. Telegram says that its moderation is “within industry standards”, but this week we have seen evidence to the contrary related to an area of criminality far less visible (and one I did not search for) – child sexual abuse material. Ever since the launch of the Silk Road marketplace in 2011, there has been a steady conveyor belt of websites selling illegal goods and services.
#DARKWEB – Telegram Channels, Groups And Bots
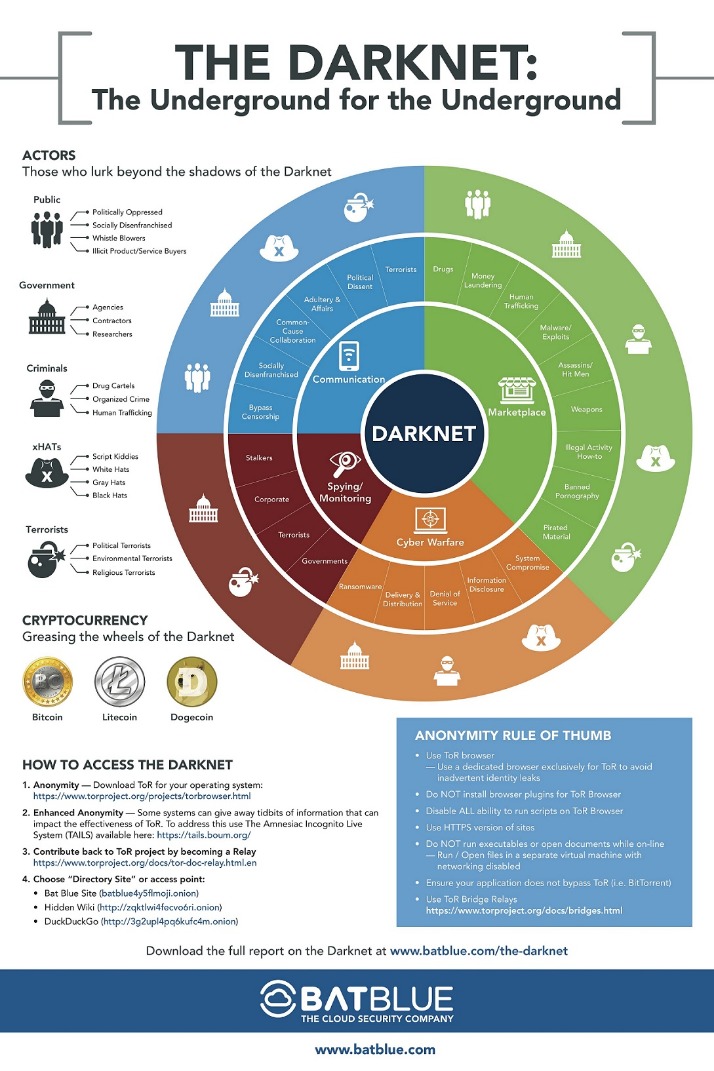
These channels serve as underground marketplaces for various illegal activities, including the distribution of stolen credentials. By breaching the security of infected devices, they gain access to valuable data such as browser fingerprints and login credentials. Infected devices and illicit Telegram channels are intricately connected as threat actors exploit these channels to distribute malware and steal sensitive information. However, no platform is completely immune to threats, and Telegram users should be aware of common threats that can potentially compromise their privacy and security. Dark web forums allow users to interact with like-minded individuals, creating an interconnected network of cybercriminals seeking to facilitate their illicit activities. These underground forums enable users to buy, sell, and trade various hacking tools, malware, or even services such as DDoS attacks or password cracking.
Dark Storm Team: Hacktivism And Large-Scale Cyberattacks
The end-to-end encryption employed by Telegram ensures that messages exchanged between users are secure and cannot be intercepted or deciphered by third parties. Consequently, this aids in preventing various illegal activities, including drug trafficking, identity theft, and online fraud. It also allows organisations to proactively detect security vulnerabilities and mitigate them before they are exploited. This knowledge enables them to fortify their defenses against potential attacks, thereby reducing the risk of data breaches. By closely monitoring dark web forums, businesses can gather critical information about evolving cybercrime tactics and techniques.
Channel Name: StarLink Cloud

With corporate devices, malicious actors can gain access into companies’ environments. For example, we found a channel with a $100 per month subscription that promises a minimum of 1,000 new logs per day. This way, they can have access to fresh stealer logs without waiting for autoshop sales.
Inbox @xnethackers for all hacking related and recovery services. At several festivals in the north-west of England last summer, more people presented to welfare services on ketamine than for other popular drugs such as MDMA.” Using data over the past year from over 1,300 different drug seller listings on the encrypted messaging app in the UK, the average price for a kilo of cocaine fell from £36,000 in April 2022 to just under £29,000 in April 2023. Within these groups, you can access links to various communities, supergroups, and chats focused on Telegram groups related to drugs . These groups act as self-regulating mechanisms within the illegal marketplace, allowing users to exchange reviews, share scam experiences, and even offer ratings for different sellers.
Having to register a domain to offer services and tools for sale makes threat actors’ operations vulnerable to distributed denial of service (DDoS) attacks that can take them offline. The hackers posted stolen sensitive data on the platform, claiming to have exploited the company’s weak cybersecurity. Based on Telegram’s data, more than 14 million groups and channels have been blocked by the app in the first half of 2025 alone.
The user-friendly interface ensures that users can quickly understand how to use the various features and functions of the app, eliminating the need for extensive technical knowledge. With its clean design and straightforward navigation, even users with limited technical skills can easily navigate the app. Telegram is a cloud-based messaging app that allows users to send messages, photos, videos, and documents securely.
Leveraging these tools like Lunar ensures you can detect, prioritize, and respond to cyber threats more efficiently and effectively while maintaining visibility even as threat actors raise and close channels, go private, or migrate to new platforms. Dark Web Monitoring platforms are necessary to track activities on Telegram because they continuously scan and monitor across Telegram at scale (tens of thousands of channels) which is also then analyzed to identify and summarize threats in real time. These stolen credentials are then sold or shared within illicit Telegram channels, providing easy access for cybercriminals to exploit their victims. Criminals on deep and dark web hacking forums use Telegram as an auxiliary communication platform, which we know because they discuss Telegram channels and share their handles in their forum posts. This helps others understand and manage the pirated media more effectively.In Pirated Software channels, educational exchanges are common, with users sharing technical information about software modifications.
The nature of content in these channels, often involving highly sought-after materials like new releases or software, increases its likelihood of being widely shared. Engagement-boosting channels often share services or content that remain relevant over extended periods, diminishing the need for constant updates. To compare the growth of these channels over time, we conducted Wilcoxon’s rank-sum test (Woolson, 2007) between different CACs (e.g., copyright media vs. leaked credentials) on a weekly basis. Cybersecurity training channels, which share content primarily via YouTube, also had fewer phishing URLs due to community engagement that helps expose malicious content. Copyright infringement media and software piracy channels had the largest share of phishing URLs, with 1,507 and 1,110 respectively.
Through this proactive surveillance, organizations can protect their data, reduce exposure, and strengthen their defense against cybercrime. It allows organizations to detect breaches, identify threats, and anticipate attacks before they cause real damage. To mitigate these risks, Dark Web monitoring has become a critical cybersecurity strategy.
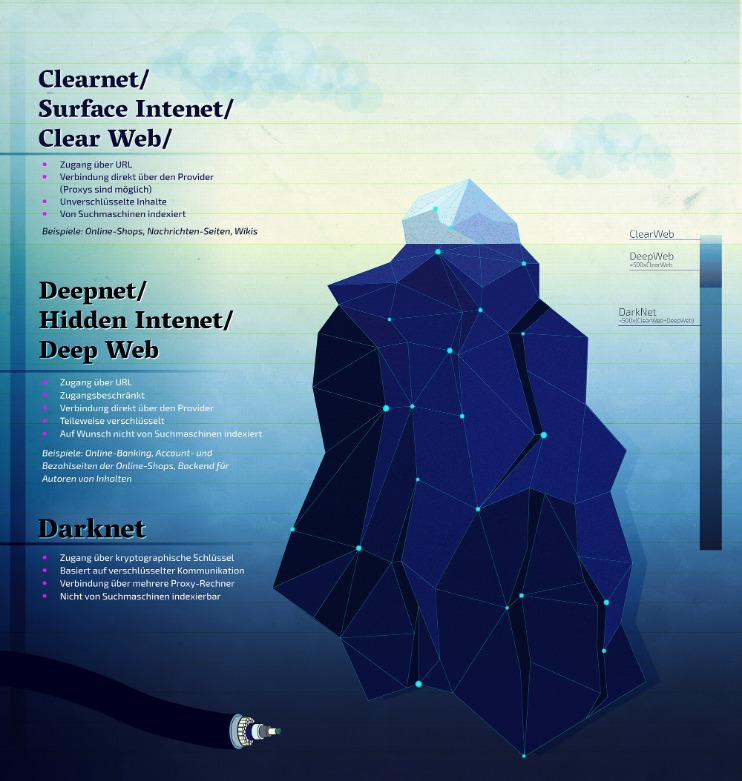
Telegram’s dark web channels are private or invite-only messaging groups, in which users chat, share information, or otherwise collaborate between themselves. This also allows Telegram’s users to utilize features such as self-destructing messages, so called “secret chats,” and groups which the platform’s visitors can access anonymously. In this article, we explain the concept of Telegram’s dark web channels and their impact in fostering new cyber threats for businesses. Chat platforms and encrypted messengers are powerful tools for connection and collaboration, but they can also be exploited by criminals. The channels highlighted here reveal just how structured and widespread illicit marketplaces have become, from massive log-selling groups to region-specific carding hubs. They also advertise live scams to get access to Japanese online accounts, share tools and data, and even leak raw credit card numbers.



