
These platforms leverage advanced encryption technologies, such as Tor and onion routing, ensuring that user identities and transactions remain anonymous. The evolution of cryptomarkets has led to improved interfaces, enhanced security protocols, and a wider range of products, making them the preferred choice for many. As darknet markets continue to evolve, they are likely to incorporate even more sophisticated features, such as AI-driven recommendations and enhanced privacy protocols.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
Some dark web search engines include a manual vetting process to ensure relevance and safety. Most dark web search engines rely on these crawlers, but some also utilize manual link submission. Unlike conventional web crawlers, they have to be able to handle slower load times, inconsistent site availability, and often sparse interlinking between sites. At a technical level, these engines access the dark web using specialized protocols, like the Tor project.
What Is WPA2 (Wireless Protected Access ?
In any case, the takedown shows that even a market deeply embedded in Europe’s drug trade can be toppled. Archetyp was Europe’s longest running and bloodiest market in the 2020s. Experts expect the vacuum to be filled by smaller rings, but warned that Hydra’s end proves no market, however entrenched, is untouchable. Millions in crypto were recovered, and top Russian vendors and buyers were exposed to investigators. Coincidentally, those admins carried out an exit scam first stealing roughly $11 million in user escrow funds in mid April. On the same day, the FBI and Europol revealed they’d arrested 61 suspects and seized 50 darknet accounts worldwide.
- Additionally, the wide range of available products caters to diverse preferences, making these markets a one-stop solution for users.
- By aggregating verified links and providing up-to-date information, these lists reduce the time users spend searching for reliable markets.
- This guide will explain what darknet markets are, how they work, how to access them safely, and what to watch out for.
- If you have any inquiries regarding the dark web or are unfamiliar with this area of the internet, this is a great place to start.
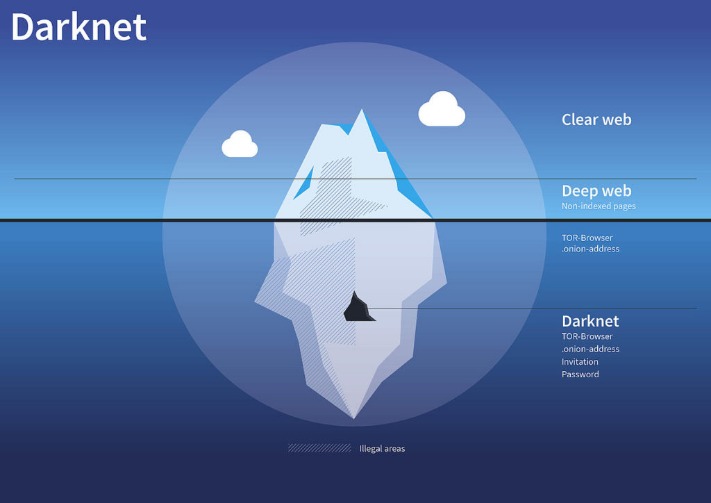
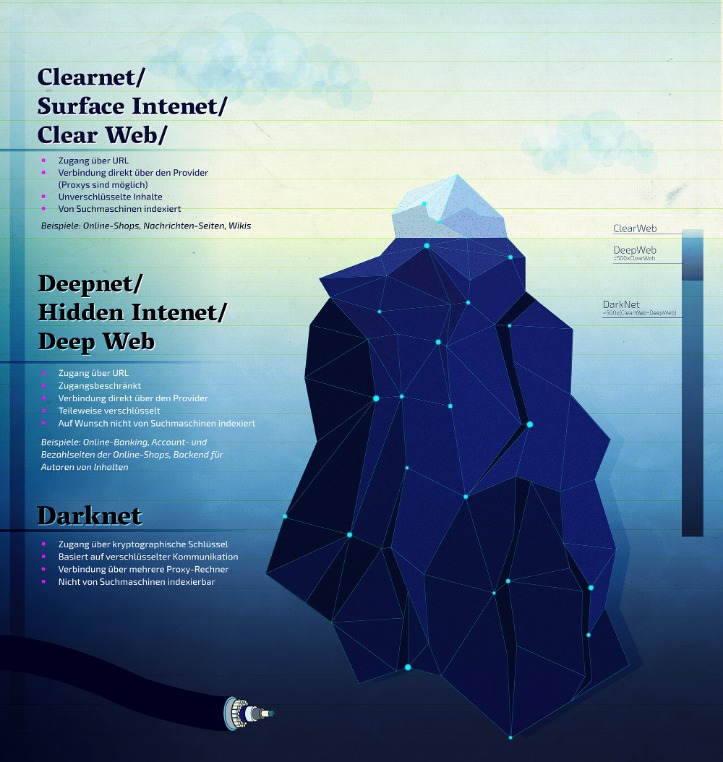
- These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers.
The BBC news website has a special .onion site, which you need to access via the dark web. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. After all, it enables users to connect and communicate with each other from around the world. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. It does not share IP addresses or web search history to protect your privacy.
OnionName — Buy Readable Onion Domains
For instance, dark web websites could be infected with malware, or designed as scams to gather stolen data. The Tor browser, short for The Onion Router, is software that allows users to access the Tor network. With cryptocurrency prices fluctuating, crypto-laundering gangs can capitalize on market volatility to conceal illicit funds, and use botnets to illegally mine cryptocurrency data. As AI becomes more accessible, hackers may use AI-driven tools to automate data theft on a massive scale. Infostealer threat actors specialize in malware that harvests personal data without consent, such as login credentials, bank accounts, and social security numbers.
Stick To Verified Onion Links
That is how one can avoid third parties monitoring their online activities. The anonymity of the Tor network becomes necessary due to growing online privacy concerns today. In recent years, several individuals have utilized the Tor browser to browse the surface of the net and explore the hidden recesses within the dark web. Some people use it for fair purposes, while others on the dark web carry out illegal activities. Viewing and navigating the dark web is not illegal.
OnionLinkscom: Your Gateway To Verified onion Sites In 2025
The proliferation of IoT and 5G devices will provide new attack vectors for infostealer gangs. Their tools often spread through phishing campaigns or compromised software downloads, enabling crimes such as identity theft. However, rivalries over dark web marketplaces could also lead to turf wars, disrupting their operations and creating new risks for businesses. In 2025, state-sponsored actors are expected to continue using the dark web for politically motivated cyberattacks. Unlike Chrome, Bing, or Firefox, people can’t access the dark web without certain software or configurations.
With these in mind, let’s take a closer look at the dark web sites rundown. Hackers, both white- and black-hat, can also be found scouring the depths of the dark web for things like malicious code, special hacking tools, victims, and more. A little refresher on the dark web – it’s like a gathering house, where all sorts of people congregate.
The 10 Best Dark Web Search Engines In 2025
Remain open to adopting these methods—be it new cryptographic tools or updated verification services—and adjust your approach as the environment shifts. While no list is infallible, starting with respected directories offers a better baseline than random search results. To safeguard yourself against phishing, fraud, and other threats, it’s crucial to verify the authenticity of links before engaging with any dark web platform.
Report It To The Authorities (if It’s Safe To Do So)
In 2025, the darknet continues to provide a secure and efficient platform for the drug trade, offering users unparalleled privacy and convenience. The combination of Tor markets and cryptomarkets has created a robust ecosystem where users can trade drugs with confidence, knowing their identities and activities are protected. The top darknet markets in 2025 feature user-friendly interfaces, streamlined navigation, and comprehensive product listings.

How To Stay Safe On The Dark Web
While this filtering is intended to improve user safety, it can also prevent access to content that is relevant for research or dark web activity monitoring purposes. However, many present uncensored search results in their rawest form and expose users to a flood of stolen data, compromised credentials, and black market activity. Click its “Onionize” button to search the onion links for any other dark web websites. Whether users are searching for alternative communication tools or exploring decentralized financial services, OnionLinks provides a direct, user-friendly route.

When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser. People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden. ProPublica aims to bring controversial, repressed stories into the open for all to see.
The market organizes everything clearly, more likely in an attempt to help newcomers (we should rather say criminals) find what they need easily. Operating more like a legit e-commerce platform (surprisingly), the market operates a 14-day escrow system, but it lets you opt for Finalize Early (FE) if you trust a vendor. Its intuitive interface and advanced search features make it easy to find local and global products. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. We recommend using NordVPN as it offers top-notch security features, including dark web threat protection. It also masks your IP address, making it difficult for government agencies to monitor or track your activities.



