
Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it. Don’t download anything unless you’re absolutely sure it’s safe. Fake sites are everywhere, and even a one-character difference in the URL can land you on a phishing page. Screen dimensions are a known fingerprinting vector.
Can You Use The Tor Browser On A Mobile Device?
Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity. Access to “.onion” domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only. People often have bad feelings about the dark web, but not everything on it is illegal or dangerous.
- If you want to improve your security further, you could also use a VPN at the same time as Tor.
- The dark web is a subset of the deep web, which includes any online content not visible on normal search engines, such as private databases and personal email accounts.
- You can, technically, but Tor warns about the lack of top-level security that this browser has.
- We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety.
- If you know any of them, you can access them safely through Tor but try not to wander off.
Is Accessing The Dark Web Illegal In India?
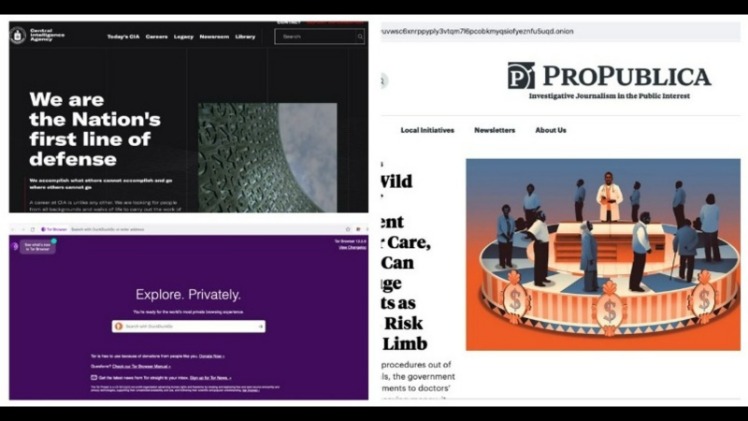
However, some Tor users do so to facilitate illegal online acts. These are only a few of the .onion search engines that are available. DuckDuckGo offers an .onion version of its search engine, while Sci-Hub offers access to millions of scientific articles and papers. We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention. In addition, NordVPN offers Onion over VPN (think Tor over VPN), which routes your internet traffic through one of its servers, passes it through the Onion network, and then sends it to the internet.
Choose A VPN That’s Good For Accessing The Dark Web
As long as you are vigilant about your online activity, there aren’t any issues. The RAT allows its creator to hijack your webcam and spy on you through your device’s camera lens. Although you plan to remain anonymous, slight human errors can crack your anonymity if you are not vigilant enough. Even if you are not a customer of illegal marketplaces, visiting them can get you on a government watchlist. Most illegal dark web marketplaces, such as the Silk Road and various open forums, remain under surveillance.
How Long Does It Take To Learn Cybersecurity? A Beginner’s Guide To Ma
Other options are the Freenet and I2P (Invisible Internet Project) peer-to-peer networks, both of which provide censorship-free communications. This prevents the node operator from detecting your IP address or from finding out any other information. All data is routed from the exit node through a secure VPN connection. Your ISP won’t be able to see your Tor network activity. This means that all of your traffic, including your Tor Browser activity, is protected.
Maintain Anonymity
I2P aims at protecting communication monitoring by third parties and from dragnet surveillance. If not, you can simply do the same as in our previous entries, and just add .cab to the end of a .onion link. Simply add .nu at the end of a .onion link, and it will take you to the website that you wish to visit. All you need to do is add “.to” to the link of the .onion website and it will take you there. Someone who is monitoring your connection will instantly see what you are up to, where do you go, and what do you do.
How To Watch Australia Vs India Live Streaming Tonight Free And Legal
Infiltrations can put you at risk of monitoring for other types of activity as well. Even if you never make a purchase, you could be watched and incriminate yourself for other activities later in life. Any online activity can carry breadcrumbs to your identity if someone digs far enough.
As well as attracting cybercriminals who use the anonymity it provides to offer hacking and phishing services, the dark web is awash with illicit forums, malware, and other potentially dangerous content. You can access the dark web quickly and easily using Tor Browser, which is specifically designed to anonymize web traffic by routing your data through multiple encrypted server “nodes,” which helps provide secure access to the dark web. Without a VPN, your ISP or network administrator may be able to detect, monitor, or block dark web access; Tor-over-VPN provides an extra layer of privacy.
- You can access these websites without worrying about someone snooping on a Tor exit node, offering more private browsing of what is known as the deep web.
- Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions.
- However, unlike Facebook, the DWSN requires users to remain anonymous and not reveal personal information to protect their privacy.
- It accounts for around 90 percent of websites, by some estimates, so we’re talking about a substantial chunk of everything that’s online.
- Sure, you’ll find a fair share of illegal activities and dubious marketplaces, but the dark web is also home to a variety of content that isn’t inherently evil.
- Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe.

Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. For journalists, students, researchers, and security professionals, it’s a powerful tool when used ethically and safely. You can’t search for .onion sites using Google. These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with.
Some hospitals even have classified medical records you can’t access just like that. The same goes for private networks belonging to companies and other entities. They have their Gmail inboxes accessible only to them. Funnily enough, the deep web is the largest part of the internet. We’ll tell you that the deep web is accessible through conventional browsers. For now, it’s vital to get the principle right.
Attackers can use tools like keyloggers to gather your data, and they can infiltrate your system on any part of the web. The dark web is filled with information theft from malware-infected users. Antimalware and antivirus protections are equally crucial to prevent malicious actors from exploiting you. Leaks of personal data can also lead to damage to your reputation via social fraud.
If you’re feeling chatty, you can always access a chat room. My advice to you would be to stick with the editor’s pick. Well, now it’s time to fire up Tails and do a little bit of tinkering. For this tutorial, I’ve used Universal.
The deep web includes both legal and illegal content, including the portion known as the dark web. This is below the surface web and accounts for about 90% of all websites. The darknet is a private place where nobody can intercept, monitor, or steal anything online from you.



