
However, remember you must use the Tor browser to access them. You can choose the best darknet (.onion) website that suits you and start surfing. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Although the underground internet world is rife with everything bad, it also hosts positive elements.
Dark Web Sites Links List

The listed links were well-grouped for a simpler browsing experience. If you are familiar with Quora and Reddit, Hidden Answers is the dark web’s version for its users. When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser. People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden. ProPublica aims to bring controversial, repressed stories into the open for all to see. For individuals in locations facing strict restrictions or those under oppressive governments, ProPublica is the perfect platform to share their stories.
- You can access thousands of issues, from the most popular to the most niche.
- Beyond network-level anonymity, technologies like SSL/TLS (Secure Sockets Layer/Transport Layer Security) are crucial.
- Artificial intelligence will play a growing role in mining hidden data for insights—provided that privacy is respected.
- Cybercriminals use the dark web to buy and sell everything from banking login credentials to large-scale financial fraud schemes.
- The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity.
Authentication systems ensure that only authorized users can access specific content. Even government websites, health portals, and legal document repositories use the Deep Web. Many sites use this file to intentionally exclude sensitive or irrelevant content from search engine results. Moreover, some websites generate content dynamically in response to user queries. These search engines use automated bots called “crawlers” to discover and catalog content across the web.
Social Media: Boon Or Bane? Delving Deep Into The Debate
- Proactive organizations are now tracking these discussions, closing security gaps in their loyalty programs and monitoring accounts for suspicious activity before fraudulent redemptions occur.
- One of the biggest and most persistent threats to banks and financial institutions is ransomware.
- Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.
- While the mere use of the deep web is not illegal, certain activities, such as accessing or distributing copyrighted materials or illegal content, can lead to legal problems.
- You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
GlobaLeaks is an open-source platform designed for NGOs and media to create customizable submission portals, emphasizing decentralization and anonymity. OnionShare is a popular open-source tool that allows users to share files securely and anonymously via Tor, widely used by activists and journalists for confidential document distribution. For developers and site operators, hosting on the dark web requires privacy, uptime, and resistance to attacks. These services form the communication backbone for sensitive conversations in high-risk environments.
Secure Your System And Mental Well-being
Alarmingly, the dark web has fueled the spread of Ransomware-as-a-Service (RaaS), where malicious actors of various levels can purchase ready-made ransomware instead of creating their own. Cybercriminals use ransomware to encrypt a victim’s data or systems, only offering the decryption key in return for a hefty ransom. Ransomware attacks have surged in recent years, with financial institutions among the favored targets. Once inside, they can capture keystrokes, hijack transactions, or create a backdoor for future access. Stolen data—ranging from customer’s personal information and credit card details to internal corporate data—is a hot commodity on the dark web. Malicious threat actors also sell login credentials to banking app accounts with funds in them.
This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity. After all, some websites on the deep web are like those on the open internet, except that they are hidden behind a paywall or protected via passwords to limit access. Some content and services on the deep web are indexed by search engines, but paywalls or password protection prevent access. It’s a place where you’ll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. The darknet, also known as the dark web, is a hidden part of the internet that cannot be accessed via normal search engines such as Google or Bing….
Don’t Install Extensions
To access the dark web, you need an anonymizing web browser or any browser that supports the Tor network. The most prevalent illicit products are pharmaceutical and recreational drugs, followed by stolen data, online bank account credentials and credit card numbers. Keep in mind that in some regions like China and Russia, it’s illegal to use anonymizers.
Use A Trustworthy VPN (But Not Just Any)
When you log into your Gmail account, access your university’s course management system, or check your bank balance, you’re diving into the Deep Web. Search engines also avoid indexing content blocked by a file called “robots.txt,” which tells crawlers what not to scan. These platforms don’t display a static set of pages; they generate results on-the-fly when you enter search terms. In practical terms, every time you log into your email, check your health information through a portal, or view your private cloud documents, you are accessing the Deep Web. The Deep Web consists of content that lives behind these barriers. However, crawlers can only access pages that are publicly available and not restricted by login credentials, paywalls, or technical barriers.
Scam Links, Phishing Clones, And Honeypots On The Hidden Wiki
The Tor Project’s official onion site offers secure downloads of the Tor Browser and developer resources, helping users access and contribute safely to the Tor ecosystem. Many people seek it out for privacy and anonymity, as the Tor network and the Hidden Wiki help mask identities and activities from surveillance. The Hidden Wiki plays a crucial role by listing verified onion links, warning users about scams, and giving descriptions to help them make informed choices. This data store also sells Paypal accounts and full dumps of financial PII (see in the image below).
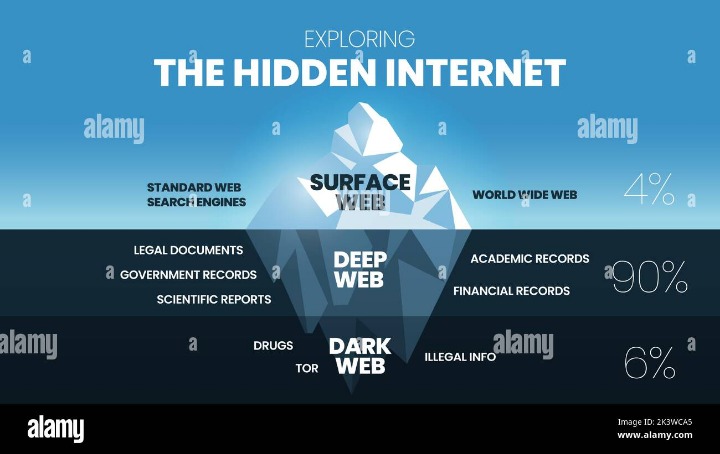

Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. When used in unison, these tools seal the security and privacy vulnerabilities of the Tor network, keeping you anonymous as you roam the streets of the dark web. The endless list of illegal activity on the dark web casts a grim picture of this part of the internet and leaves the impression that it’s dangerous.
While using the Tor browser, you can click links to .onion addresses and they’ll load normally. It’s a modified version of Firefox that’s configured to connect to sites through the Tor network. To access a .onion address, you’ll need to access it through the Tor Browser.
Risks And Dangers Of Financial Services On The Deep Web
Above all, keep your Tor Browser and security software updated, and use privacy-focused browser settings to minimize exposure. Avoid clicking on links posted in random or unmoderated sections, as these are often the most dangerous. Another good practice is to cross-reference links with multiple sources to confirm consistency. Because the Hidden Wiki aggregates many links, it often contains outdated or malicious URLs disguised as legitimate ones. Dark web sites linked through the Hidden Wiki offer forums for free speech, whistleblowing platforms, and uncensored news outlets that operate beyond the reach of traditional censorship mechanisms.
One of the cases that brought dark web activities to public attention involved Ross Ulbricht, who in 2013 was arrested by the FBI. The TOR project released publicly in 2004 and is the most popular publicly available dark web access forward. On March, 20, 2000, a peer-to-peer, decentralized network known as Freenet was released and marked the first recorded instance of the dark web, which was commonly referred to as the darknet. Example include bank account information, insurance records, or subscription-based content. The publicly indexed part of the web, known as the surface web, consists of approximately 4-5 percent of the internet. He held multiple compliance AVP roles at HSBC and is a published author, speaker, and anti-financial crime thought leader shaping the best practices in the field.
Shift Left In Cyber Defense
This duality allows users to choose whether to access the platform openly or anonymously. But we are on the dark web, you can’t trust anyone, so there may be sites containing illicit content. But if you are thinking you can find links to the deepest part of the dark web using this site, it’s not that simple. On Hidden Wiki or other darknet wikis such as OnionWiki, you can find working links to sites like Awazon, ProPublica, Facebook, Deep Web Radio, and more.
It allows you to search for images, maps, files, videos, social media posts, and more. SearX is a metasearch engine that you can use on the clear web and dark web. Visiting the links from specific questions may be a bit safer.



