Individual users lack the contextual data and tools to penetrate dark web defenses. Site owners use the robots.txt file to redirect search engines and avoid excessive traffic. Deep web content includes data stored behind log-in portals or paywalls. In the process, search engines miss a huge amount of data. Standard browsers can access most internet content, even if it does not appear in Google results. To be part of the dark web, sites must be invisible to a standard web browser and search engines.

Myth 1: The Dark Web Is Only Used For Illegal Activities
Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information. However, not all the forums and social media sites are legal on the dark web and often include shocking conversations and pin boards by anonymous users. The dark web offers a marketplace section where users can buy legal or illegal products. The dark web is a subset of the deep web that is intentionally hidden and requires specialized tools such as Tor, I2P, or Freenet.
If you need to access dark web resources, these are the steps you need to take. There are many legitimate uses for dark web services and communication. To access a dark web address, you must use a VPN and a suitable browser (it should be Tor). Drugs, weapons, and stolen IP and data are all hot businesses on the dark web, with terabytes of information on offer. ZDNET’s most up-to-date cybersecurity guides deliver practical tips to stay safe and productive today amid the ever-evolving threat landscape tomorrow. We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media.
Uncovering Hidden Threats With Dark Web Monitoring
No one can prevent all identity theft or monitor all transactions effectively. Full access to plan features depends on identity verification and credit eligibility. Aura’s services may not provide the exact features we write about, nor may cover or protect against every type of crime, fraud, or threat discussed in our articles. You don’t have to become a cybersecurity expert to understand the mechanics of the Dark Web. Once it’s out there, you cannot reverse the process. There is no reliable method of removing your data from the Dark Web.
- As FBI Deputy Director Andrew McCabe said after AlphaBay was shut down, We will find and prosecute criminals wherever they operate, even on the dark web.
- When you use Tor, your internet traffic is routed through a series of volunteer-operated servers, encrypting and bouncing your connection across the globe, making it difficult to trace your identity and location.
- These sites bypass copyright protection and may be accessed only on the Dark Web to avoid legal scrutiny.
- Cryptocurrency enables buyers and sellers to exchange goods and services without revealing their identities, making it ideal for illegal activities.
- With tools like StealthMole’s Credential Lookout or Darkweb Tracker, you can safely check if your data is available on the dark web.
- Such architecture helps websites and services obscure their physical server locations.
Don’t Get Hooked How To Spot And Stop Phishing Attacks
Get seamless security integration for MSPs with NordLayer, SentinelOne & Proofpoint. Discover the success stories from various sectors, illustrating our impact on partner and client growth. Join NordLayer’s Referral Program to offer leading cybersecurity solutions & earn rewards. Elevate your offerings with top-tier cybersecurity, enhancing service quality and profitability Introductory resources for industry terminology and frameworks
Searchlight Cyber

These techniques, over time became public and thus led to the emergence of the hidden networks. The dark web is a domain that provides anonymity to site owners and guests so they cannot be monitored by outsiders. The Dark Web is said to be 5,000 times bigger than the surface web, and yet, it cannot be accessed through a normal browser or a search engine.
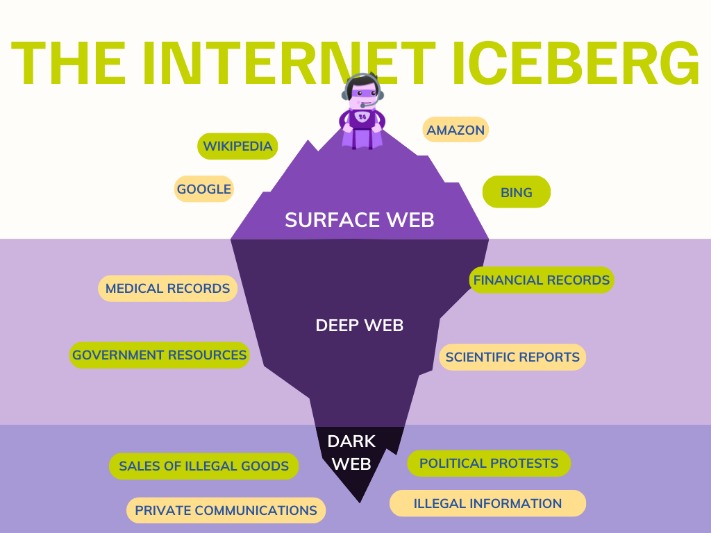
Because it’s such a big part of internet activity, it’s worth noting how this Dark Web browser works and why it exists. While no one can pinpoint the origins of the Dark Web, it’s now referenced in mainstream conversations about technology and digital security as the seedy source of many security issues. The Deep Web hosts information that usually requires a username and a password to access, mainly for security and privacy-related reasons. Because not all the information you can access online belongs in the public domain. This specialized browser grants users a level of anonymity that is especially appealing to cybercriminals, hackers, and government operatives who want to hide their identity.
The dark web isn’t entirely bad, but it’s clear that it can be deeply dangerous. But, of course, exercise caution and stay away from anything illegal. You’d also enjoy anonymity and privacy thanks to Tor’s encryption and routing, something you don’t get from most normal browsers. We didn’t give them any information, but it’s scary to think how legitimate they sounded in the email.
Final Thoughts: The Dark Web Isn’t Just For Criminals

Other users appreciate the browser as it allows them to circumvent censorship. The browser isolates each website you visit, so it prevents trackers and ads from following you online. In this article, we’ll take a look at what the Tor Browser is, and how it can help you stay anonymous on the internet.
How To Access The Dark Web In 3 Steps
The sites on the Dark Web are often characterized by their .onion or .i2p domains, which are only accessible through specific browsers like Tor or I2P. In 1989, Ian Clarke launched the Freenet project, which aimed to allow anonymous online interactions at a time when internet anonymity was difficult to achieve. Many of these services are legal and legitimate, but they can host illegal content or activity. But just like when you’re online normally, the risks increase depending on what you do while visiting dark web websites. Normal sites on the deep net (like your online banking site or email account) sit behind secure logins, paywalls, passwords, and authentication forms, but you don’t need any special software to reach them. The key difference between the deep web and the dark web is that the deep web refers to all web content that requires login credentials to access, while you need special software to reach dark web content.

This high barrier entry to the Dark Web exists to protect user identities, online activities and location, and maintain their anonymity. It combines strong layers of encryption with the ability to randomly bounce internet traffic through the Tor network of relays. The Onion Router (hence the Tor acronym) uses three layers of encryption and a specific internet traffic routing mechanism to ensure complete anonymity. Many of the activities on the Deep Web involve personally identifiable information, such as medical and legal documents, financial records, academic research, intellectual property, confidential commercial data, and more.
Indeed, cyber breaches have shown us that any backdoor or weakness can be found and exploited by hackers in order to steel people’s information, pictures and data. Another issue for law enforcement is that – like most things – the dark web and its technologies can also be used for both good and evil. It is not surprising, then, that the dark web is often used for illegal activity and that it is hard to police. So just for a minute imagine that the whole internet is a forest – a vast expanse of luscious green as far as the eye can see. This tactic can uncover plans for future attacks, identify key threat actors, or reveal supply chain compromises.
What Is The Tor Browser, And How Does It Help Anonymize Browsing?
The term “dark web” often brings to mind shady back alleys of the internet, a place where hackers and criminals lurk in the shadows. But navigating the dark web is full of cybersecurity and legal challenges. It does support whistleblowers by offering them anonymity and secure communication in an oppressive regime. Therefore, you should understand the legal risks of accessing the dark web before you venture into this murky world. Accidentally downloading or viewing illegal materials may result in severe legal consequences.
Small Business Trends is an award-winning online publication for small business owners, entrepreneurs and the people who interact with them. Small businesses should implement strong cybersecurity measures to mitigate these risks. Knowing how these tools work is essential for safeguarding sensitive information. It exposes them to potential risks like malware and ransomware, allowing them to take proactive steps to protect sensitive data and ensure legal compliance. Understanding the dark web helps small business owners enhance their cybersecurity measures.
Initially designed for secure military communications, it evolved into a broader tool for online anonymity, later expanding to public use with the Tor network. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web. Many dark internet users favor Tor which uses a network architecture originally developed by the U.S. Unlike traditional browsers, this will route your internet traffic through an anonymizing network and mask your IP address. The dark web is a small, hidden subset of the deep web that requires special tools to access.



