You can also use Tor to enjoy better privacy online, but I honestly think a VPN is better suited for that. Repeat this process until you get an IP address from your desired country. You can now start surfing the web while connected to the Tor network. While Tor is legal in most countries, it can also be used for illegal purposes.
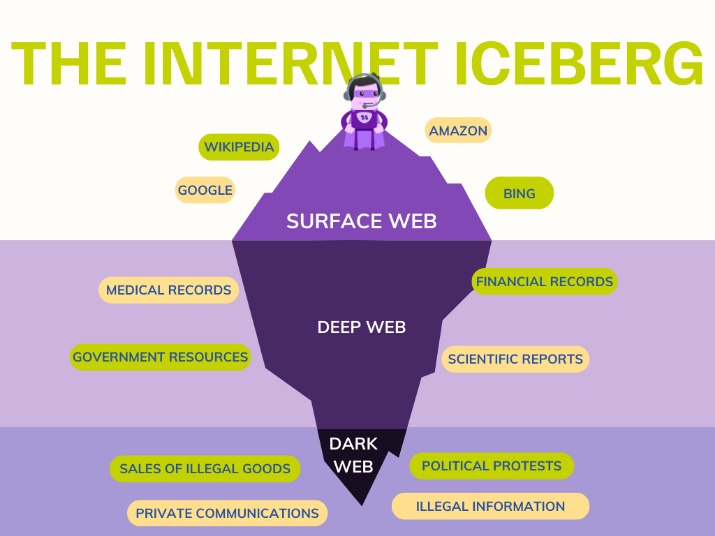
Myth 6: More Than 90 – 96% Of The Internet Is Made Up Of The Dark Web
If you need to access dark web resources, these are the steps you need to take. There are many legitimate uses for dark web services and communication. Drugs, weapons, and stolen IP and data are all hot businesses on the dark web, with terabytes of information on offer. When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies.
Install A Virtual Private Network (VPN)
If you’re curious about exploring the dark web for legitimate reasons, safety should be your top priority. In countries with strict internet censorship, the dark web can be a lifeline. Engaging in any of these activities is a serious crime with severe consequences. However, what you do on the dark web can certainly be illegal. This makes it nearly impossible for anyone to trace your online activity back to you.

Risks And Essential Tips For Safe Browsing On The Dark Web
If you need an idea of where to start, check out our list of the best dark web sites in 2025. Instead, you’ll use specialized search engines to find them. Tor isn’t available for iOS due to Apple’s restrictions, but you can still access the dark web on your iPhone using the Onion Browser, which is from the Tor Project. To access the dark web, you’ll need to use a dedicated browser — Tor on Android or the Onion Browser on iPhone.
How To Access The Dark Web On Android
- Discovered pages are indexed in an extensive database and ranked based on numerous factors.
- Although browsing the deep web poses no particular danger, it is still best to exercise caution.
- You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions.
- Tor Bridges or a VPN will help you to use Tor privately, as your ISP (Internet Service Provider) will not see that you’re connected to a Tor node.
- A bridge creates an obfuscated relay on the Tor network that is not listed in the main directory.
- This is where all the cat videos and trending YouTube songs live, easy to find and access.
Authorities use infiltration techniques and metadata analysis to identify and prosecute offenders. Many marketplaces and services operate without oversight, making fraud rampant. Without proper defenses—such as running the browser in a virtual machine or using read-only operating systems—users risk compromising their devices and identity. Cybercriminals often design traps to steal data or infect systems. Visiting the dark web carries significant risks, especially for users unfamiliar with its structure and threats. The anonymity of cryptocurrencies and direct user connections makes it a lucrative ecosystem, powering both small-scale attacks and large ransomware campaigns.
Private Internet Access even offers the Shadowsocks proxy for added security. ExpressVPN is slightly expensive but a trustworthy provider for risk-free dark web browsing. Its Advanced Protection also blocks malicious sites, trackers, and ads. Its RAM servers and Private DNS go a step further to protect your identity online. Like NordVPN, this provider doesn’t store logs and has around twenty third-party audits to prove it.
Each network has its strengths, drawbacks, and intended use cases. The concept of a decentralized web, championed by technologies like IPFS (InterPlanetary File System), focuses on distributing content across multiple nodes rather than relying on centralized servers. I2P is an anonymous overlay network designed primarily for peer-to-peer applications. While Tor is the most well-known option, it’s not the only one. Exploring the Dark Web introduces risks that extend beyond network-level tracking. Before you embark on your journey into the Dark Web, it’s crucial to establish a secure foundation.
Can You Use The Tor Browser For Torrenting?

The dark web is just one of the three main layers of the internet. But, for anonymity to really work, Tor needed lots of people using it, not just spies and their handlers. Instead, it uses its own search engines – we’ll get to that later. We’ll also share some tips for protecting your personal data if you decide to explore it. To fully understand what the dark web is and whether there’s any reason for you to go there, we’ll break down the different layers of the internet and how they relate to one another. But the truth is, that’s only one “dark” part of the story.
Cybersecurity Best Practices For Protecting Your Digital Assets
- Unfortunately, it’s slower than the previous two VPNs, but its performance is admirable in practice.
- The only benefit is that the ISP won’t know you’re using a VPN.
- If you use the right tools, like Norton 360 to protect against malware and phishing, stick to trusted sources, and avoid suspicious sites, your risk is much lower.
- While some can simply install and use the Tor browser like any other, there are a few complications for those in countries where Tor is blocked, on corporate or university networks where it’s banned, or where more security is needed.
- Installing the Tor Browser is the best way to access the dark web.
The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. For a number of technical reasons, it’s much faster and more reliable than Tor. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous.

It provides great privacy and security, and it’s good for secure streaming, torrenting, and gaming. A VPN is an online app that also changes your IP address and encrypts your traffic — but it only does it once, which allows VPNs to provide much faster speeds than Tor. When you use the Tor network to access a site, your traffic is routed through at least 3 Tor servers, which are also called “relays” or “nodes,” and are usually run by volunteers. The Tor browser is a popular way for internet users to visit dark web sites.
The Best Dark Web Search Engines In 2024
Use VPN, avoid logging into personal accounts, enable Tor security settings, and stick to trusted sites. While difficult, tracking is possible if security measures are misconfigured or if users reveal personal information. Check onion links through trusted directories, user reviews, and reputation checks.
For this tutorial, I’ve used Universal. It’s like in those movies where the doctors are experimenting on deadly viral strains from behind the safety of a glass enclosure. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node.
Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands. Install Avast SecureLine VPN for Android to protect your privacy and keep your data from falling into the wrong hands. Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands.



