
When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously.
- In fact, it now features more than 11,600 illegal items, which include hacking tools, hard drugs, and all types of cybercrime services.
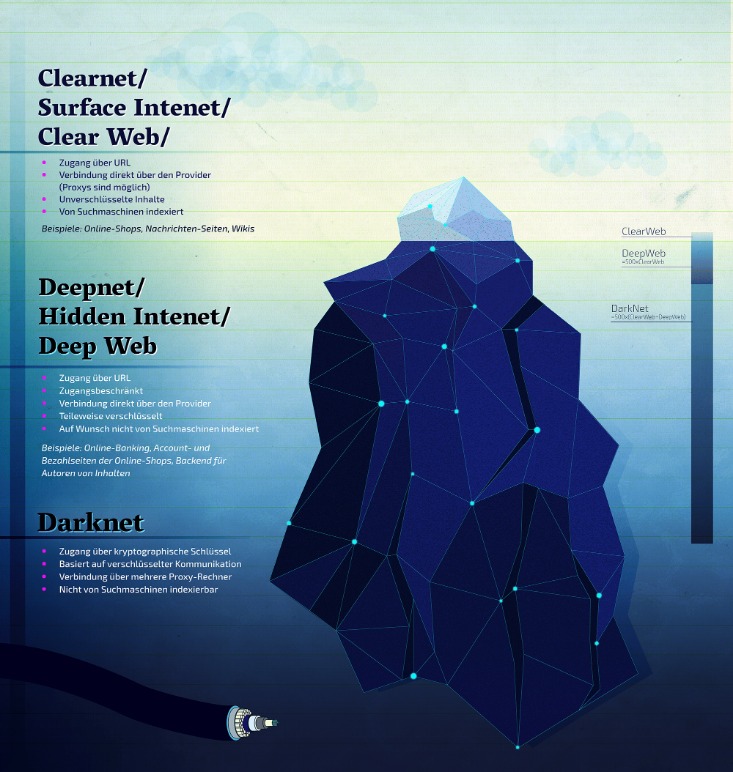
- The Dark Web, on the other hand, is a small fraction of the Deep Web that is purposefully concealed and can only be accessed with specialist software such as Tor.
- It knows you’re accessing Tor but can’t see beyond that.
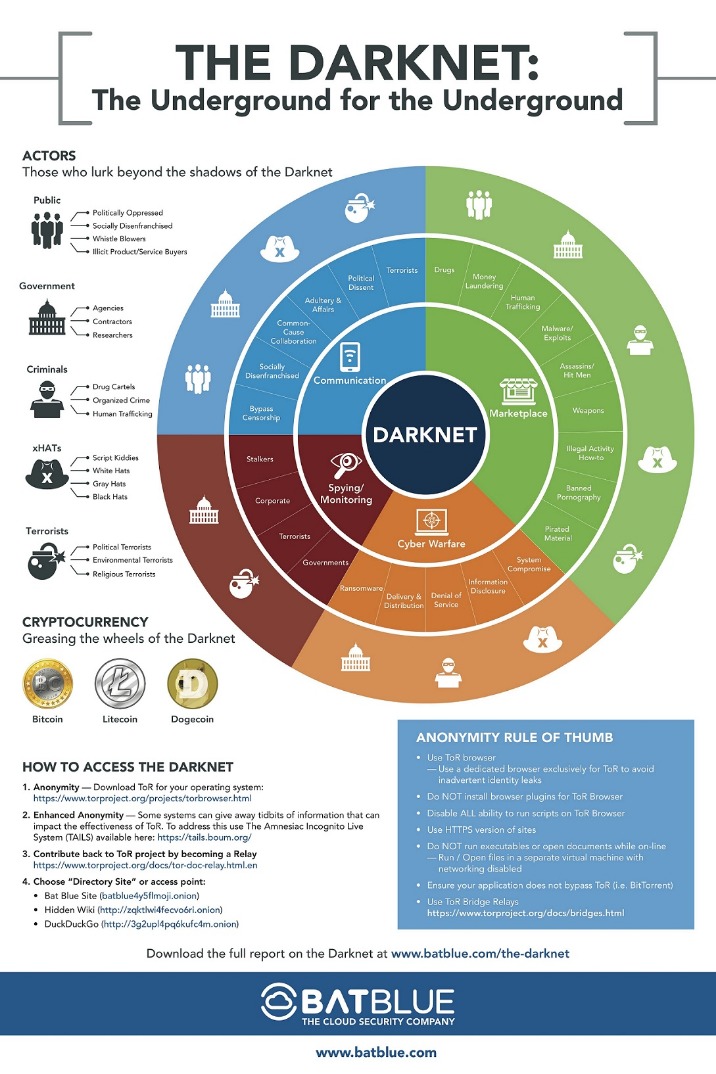
- The darknet has been a realm filled with both intrigue and controversy, a space where anonymity reigns and transactions often occur under shady auspices.
History Of Darknet Markets
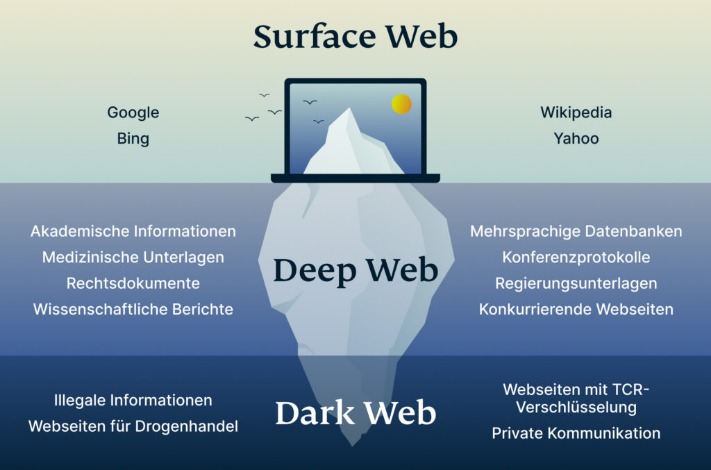
This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software, configurations, and authorization to access. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network.
Top Darknet Markets 2025
This means it’s sometimes possible to buy these currencies (such as XMR) in exchange for fiat (GBP, USD, AUD, etc), but you may find yourself prevented from transferring such currencies outside of the platform you’ve purchased them from. This is why there’s no specific endorsement for any particular marketplace I can make, but I’ll include a few of the most common below for reference. Some get hacked, some get shut down by law enforcement, and some succumb to their own greed – whereby the operators ‘exit scam’ entire communities. There are hundreds of marketplaces to choose from, each with their own set of communities, politics, and socio-economic motivations.
How To Use Tor Browser Safely

The book follows the chilling true story of the decade-long quest to take down Paul Le Roux. (Forget what you think you know.) Instead, they offer a peek into the minds of the people who actually navigate this hidden digital realm and explore the real-world impact it has on our society. (Let’s face it, most people just think of illegal stuff and shady characters.) But what if there’s more to it?
For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. Websites and data on the dark web do typically require a special tool to access. Users upload encrypted files or websites (“freesites”) that get cached and shared across the network. However, its network is still small, and there aren’t many hidden services available yet. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network. It uses its own internal DNS to access “eepsites”, not .onion addresses.
- Well-known news websites, such as ProPublica, have launched deep websites.
- Always make use of a protected VPN, never exchange personal information, and only visit reputable websites.
- It took a betrayal within his network for law enforcement to catch him.
- This is because the dark web is full of potentially dangerous content, and a VPN will help keep your identity and personal information safe.
- It’s no secret that the dark web can be a tricky and dangerous place for the general internet user.
Drughub Market
If the product or service you’re attempting to buy is illegal, you’re running the risk of arrest. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information.
Practices like search engine optimization (SEO) are specifically implemented to help websites perform well and rank higher in search engine results. This might seem strange since most people want their websites to be found through specific searches. The “dark web” refers to websites that aren’t indexed by search engines like Google and Bing. Basically, it’s a part of the internet that isn’t indexed by search engines.
Welcome To Archetyp Market
Unlike I2P and Tor, you don’t need a server to host content. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. For a number of technical reasons, it’s much faster and more reliable than Tor.
Incognito Market
This guide provides verified .onion links, market stats, and expert insights into Tor and Monero usage as of February 21, 2025. Archetyp was founded in May 2020 as an online marketplace to facilitate the illicit drug trade. They were initially impressed by the libertarian philosophy of the Silk Road marketplace, but after its seizure, many of the replacement markets they found were focused more on profit than this libertarian philosophy. Archetyp was an online drug marketplace, and only accepted drug-related listings. The Darknet is not inherently illegal, but its anonymity enables both good and bad use cases.
Dark web marketplaces often rely on Bitcoin, a cryptocurrency known for its anonymity and flexibility. The dark web’s anonymity makes it difficult for law enforcement to track down these criminal activities, leading to a rise in their prevalence. For Example, In May 2021, authorities in Germany brought down Boystown, a child pornography network with more than 400,000 registered users. Other porn-related content found on the dark web includes revenge porn and sexualized torture, and the killing of animals. Some fraudulent websites even pose as fronts for terrorist organizations like ISIL. Bitcoin allows for anonymous donations, making it easier for terrorists to fund their activities and purchase weaponry.
Tor over VPN and VPN over Tor both involve using a VPN with the Tor network, but in different orders. For example, journalists, whistleblowers, and privacy-conscious individuals often use it to communicate securely or access uncensored information in restrictive regions. The goal is to minimize any potential damage if you accidentally stumble upon harmful content or download something malicious.
Minimize Or Rescale Your Tor Browsing Window
It is notorious for illegal transactions and activities such as drug trafficking, arms dealing and identity fraud. By keeping these tips in mind and maintaining cautious online behavior, you can safely navigate the depths of the Tor network while ensuring your anonymity. This encrypts your communications with websites, providing an additional layer of security. Tor (The Onion Router) offers a means to access the internet while preserving your anonymity and privacy.
Recommended VPN Features:
From encrypted communication channels and hacking forums to illicit marketplaces, the dark web is a destination for millions of daily users. Learn more about the kinds of sites that can be found on the dark web and how you can access them. Ghost is an experienced dark web enthusiast with years of experience navigating the hidden corners of the internet.
The most common and convenient way to access the dark web is to download & install the Tor browser. Then get a VPN to encrypt all your online activity and stay safe wherever the web takes you. The dealer trend is helped by the fact that drugs on the darknet are both cheaper and more potent than what is available on the street.
These are okay, but specialized search engines are better than general ones for finding info on the deep web. Many of the best general deep web search engines, like Alltheweb, DeeperWeb, and CompletePlanet, have shut down or been acquired. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling.
Additionally, while the Tor Browser (the most common tool for accessing the dark web) has some built-in privacy and security features, it’s not 100% safe.. From these activities, the solution should be able to gather data samples, uncover motives, and help you deploy smarter cybersecurity workflows. For instance, if a threat actor is in possession of stolen data from a large healthcare provider, security personnel acting on behalf of the company are likely to conduct a large portion of that investigation throughout the Dark Web. Indeed, they must frequently be accessed by cybersecurity organizations conducting threat hunts or defending their networks or those of their clients. Many of these illegal activities use Bitcoin and other cryptocurrencies for transactions so that the sellers and buyers can remain anonymous. While the amount of traffic is small compared to the e-commerce taking place on the open web, there is no denying that the Dark Web is a haven for bad actors and illegal e-commerce activities.
The dark web isn’t only about illegal activities; its primary purpose is to provide maximum anonymity by making your connection private online through encrypted servers. This hidden part of the web carries several illegal activities, including drug and weapon dealing, pornography, private data, and more. From cybersecurity researchers to IT managers, understanding how to navigate the dark web can help monitor cyber threats, protect sensitive data, and investigate cybersecurity incidents.



