
The internet providers and websites can still see that you’re using Tor, as Tor node IPs are public. In a nutshell, the deep web is not illegal as it’s a network for privacy and security-conscious people. Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble. Privacy and anonymity are the core values of the dark web, and it hosts both harmless activities and illegal content.
How To Access The Dark Web Safely: A Step-by-step Guide
This will allow you to take action right away and reduce the risk of any further damage to your data or identity. There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return. There are numerous threats lurking in the dark web, including some very dangerous scams and malware that could wreak havoc on the lives of unsuspecting users. Again, remember that it’s best to safeguard your dark web browsing sessions with the added protection of a VPN before using any of these browsers. In fact, there’s an Android version of the Tor Browser and trusted browser apps on the App Store, too. Let’s look at two popular browsers you can use to access the dark web on desktop computers and laptops.
Top 10 Best Dark Web Search Engines In 2025 Safe &
After all, it enables users to connect and communicate with each other from around the world. The social media giant is also aware of the many attempts by repressive regimes to restrict its access. Although the social application is known for collecting data on its platform, it does not like sharing the information with others. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. It allows you to search for images, maps, files, videos, social media posts, and more.

How To Access The Dark Web On Android
Tor protects your identity inside its network, but it doesn’t hide everything. For most users, this configuration does more harm than good. With this setup, your ISP sees Tor usage, and your VPN provider sees the final traffic after it leaves Tor. It’s extremely rare and only useful in very specific cases, like if your VPN is only accessible through Tor. This method sends your VPN connection through the Tor network.
Is It Illegal To Visit Dark Websites?
This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources. Websites and pages in the deep web might include password-protected content, private forums, and personalized resources. You could consider the clear or surface web the “top” and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox. Here’s everything you need to know about this other internet, as well as how to access it. The area of the internet we access daily is known as the clear or surface web. No longer restricted to dial-up, many of us now consider access to a stable high-speed internet connection a critical element of our daily lives.
Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. If you’re lucky enough, you can find it on clearnet privacy forums. If you want to find its current links, you can search for terms like “Daniel replacement.” Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). Hence, you never know when a popular .onion site is going to vanish, or even die.
If you’re looking for a 100% free VPN with unlimited data that respects your anonymity and doesn’t act shady under the hood, Proton is your best bet. We used it to access a range of .onion sites (from whistleblower hubs to forums and file drops) and it didn’t throw a single red flag. That means you can access .onion sites without even opening the Tor browser. That said, a few standout free VPNs are safe enough to pair with Tor, especially if you’re just browsing, downloading PGP keys, or checking out .onion sites with a light footprint. It’s a corner of the internet where privacy is currency—and accessing it without protection? You can still be tracked at network entry and exit nodes, as indicated by reports that police identified Tor users by surveilling data centers.
Do Not Share Personal Information

By monitoring forums, marketplaces, and communication channels, security teams can identify emerging threats, compromised credentials, and chatter about planned attacks. The dark web plays a crucial role in cybersecurity, serving both as a threat vector and a valuable intelligence source. Lastly, we provided a list of recommended Dark Web websites, showcasing platforms and resources dedicated to privacy, journalism, whistleblowing, and secure communication. We addressed the importance of avoiding illegal activities and scams, recommending that individuals stay informed, exercise caution, and trust their instincts. In this article, we discussed the background of the Dark Web and its association with both legal and illegal activities. While it provides anonymity, privacy, and access to censored information, it is important to approach the Dark Web with caution and adhere to ethical guidelines.
This is because law enforcement often actively monitors these sites. The threat can extend to your entire network of devices connected to the internet. For example, China uses the Great Firewall to block access to Western sites. You could be monitored closely even if you are not doing anything illegal. For example, the Silk Road site operator, an illegal dark web marketplace, was traced and arrested. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.
The deep web contains material not indexed by search engines. If you ever land on a questionable site, it’s smart to check whether your data is secure. Granted, criminals do gravitate towards darknet sites in order to perform unlawful activities.
- Onion websites on the Dark Web have addresses ending in .onion instead of the usual .com or .org.
- This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources.
- Routing your VPN traffic through a Tor connection is referred to as VPN over Tor.
- Library Genesis offers a search engine for collections of books on such topics as computers, business, technology, and more.
- Check out my article for more information about the dark web and how to access it while staying safe.
- To minimize the risk, research and verify sites before visiting them.
WANT TO TRY THE TOP VPN RISK FREE?
You can check our guide on the best VPN services to find the right VPN solution to protect your privacy. It offers better speed and security than other alternative methods. You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft. However, with the right security measures and cautious browsing, you can minimize these dangers.
Even without the code, you can visit the security section to get tips on improving your daily life privacy. In addition, it ensures that no record of communication is stored. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
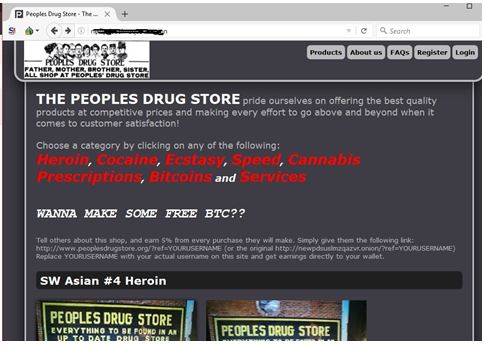
Those caught facilitating or participating in illicit transactions, such as drug trafficking or the sale of illegal firearms, face stringent federal charges. These changes aim to provide clearer guidelines for prosecuting cybercriminals and deterring illegal activities. The anonymity and encryption technologies used by dark web users complicate traditional investigative methods. Operations like “Operation Onymous,” which led to the seizure of over 400 dark web sites, demonstrate the ongoing battle against criminal content.
What Activities Are Considered Illegal?
For instance, did you know you can unknowingly break the law while browsing the internet? Clario Anti Spy’s Data breach monitor scans for known breaches tied to your email and alerts you if anything’s been exposed. Before you explore further, check if your data has already ended up on the dark web.

Why You Need A VPN To Be Safe On The Dark Web
Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination. The Tor Browser is configured to make all users look the same, making it nearly impossible for users to be fingerprinted based on their browser and device information. The browser uses a unique security system, which the United States Navy originally developed to protect the government’s intelligence communications. Suffice it to say that your Internet Service Provider (ISP) can detect when you’re using the Tor Browser, which can make you the target of increased surveillance by both the ISP and the government.
Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet. These sites are only accessible over the Tor network and are commonly used for privacy and anonymity. I2P can only be used to access hidden sites that are only available on the I2P network. The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content.
Once you have accessed the dark web using the Tor Browser, finding specific sites can be challenging due to their complex URLs and the transient nature of many dark web pages. Content on the Dark Web exists on overlay networks that use the Internet and special tools and configurations to sustain security and privacy. The terms Darknet, Deep Web, and Clear Net are often used interchangeably, but they refer to distinct parts of the internet, each serving different purposes and accessibility levels. The dark web hosts educational materials, whistleblower sites, and even mainstream media outlets, making it a valuable tool for research and information. However, engaging in illegal activities on the dark web, such as viewing child pornography, selling drugs, or participating in other illicit transactions, is against the law.



