This design philosophy minimizes user error, which is a significant operational risk in digital environments where transactions...
wpadmin
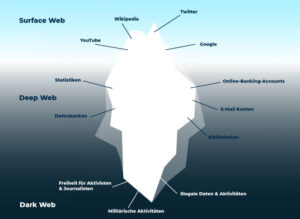
These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal...
Digital Risk Protection Threat Intelligence Dark Web Monitoring Cybersecurity Platforms Security Tools By leveraging automated dark web monitoring, organizations can mitigate...
A further PIN may be required to perform transactions, better protecting users against login credential compromise. This...
A reliable darknet URL serves as the primary gateway, and its stability is critical for maintaining access...
For a market such as Nexus, this means users can connect through multiple verified gateways. The security...
The increase has been primarily due to the emergence of fentanyl and other synthetic opioids in the...
Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user...
Likewise, law enforcement agencies each day continue to fine-tune their strategies to get past these networks. The...
Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one...